One of the most time consuming tasks when working with OS Deployment in ConfigMgr is implementing the drivers needed to support different hardware models. There are a couple of reasons for this:
- Determining if drivers installed correctly can only be determined by executing an actual Task Sequence, which takes a lot of time.
- Each Hardware Manufacturer has its own way of providing drivers. Finding the right driver can be a real nightmare and some Hardware Manufacturers make a real mess of the drivers they provide. On the other hand there are some manufactures which supply driver packages which you can import directly into ConfigMgr.
- Especially for laptops, which contain a lot of extra features in the hardware, manufactures make it a sport to keep the optimal configuration which consists of the needed drivers plus additional software as vague as possible, so it’s up to you to find out which drivers and driver applications make the laptop fully functional. Don’t we have a nice job 🙂
- Some HW manufacturers are known to change the hardware inside different batches of the same hardware model, make sure that you make agreements with your HW supplier that the HW doesn’t change with each delivered batch of machines, or you will continue to spent time on certifying HW models.
Before just simply starting I recommend you to create a strategy for implementing and maintaining the drivers within your company. What follows below are some guidelines which can help.
For implementing drivers we have several options:
- If the manufacturer provides so called driver packages, implement these drivers. It is known that Dell and HP at least provide some ready made driver packages for at least their newest hardware models.
- Use the out-of-the-box drivers supplied with your Windows by default and only use drivers downloaded from the manufacturer when needed, this is often the fastest way, but not necessarily the most stable.
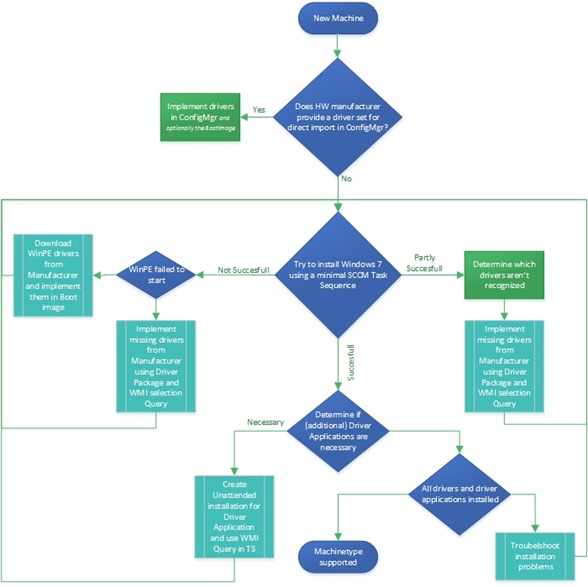
Below is a flowchart of the steps needed, when choosing to only implement drivers which are supplied by Microsoft in the Windows installation, and install additional drivers when needed.
Step 1: Determine if manufacturer provides driver package for your specific hardware model. Dell provides driver packages on a FTP download location which can be found here:
Also HP now provides these driver packages as part of the SoftPaq Download Manager, as detailed by Johan Arwidmark on his blog here
If the HW manufacturer doesn’t provide any driver packages for import in ConfigMgr
For implementing drivers, I recommend using the “Control Freak” method as described by Johan Arwidmark in the following blogarticle: The Drivers Saga continues – How to Master Drivers in ConfigMgr 2012, this methods lets you create driver packages per HW model, and use a WMI query to apply the driver package based on the detected HW in the Task Sequence.
You can determine the HW model by executing the following WMI query on that model:
Wmic computersystem get model
Step 2: Try to install Windows from your custom task sequence and see whether this installation is not, partly or fully successful.
Option A: Not successful
If the installation is not successful, the task sequence doesn’t even have a chance to start, because for example the boot image doesn’t have the necessary network drivers injected to support your hardware model. Michael Petersen has described how to add only the necessary drivers to your boot image in his blog post: Finding and adding only the correct device driver to the Boot image. Another reason for installation not to be successful is when the task sequence breaks during deployment for some kind of reason related to drivers.
Option B: Partly Successful
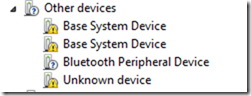
If the installation is partly successful, the task sequence probably started successfully and was able to finish as well. But you will notice some missing devices in your device manager.
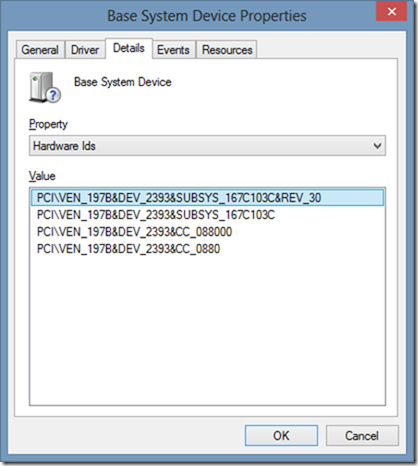
This is where the fun starts, how can i find out which driver I need to download in order for my Base System Device to start working. Well, the answer to this is that we need to find the Vendor ID and Device ID. You can find the Vendor ID and Device ID by opening the properties of the Base System Device and going to the Details tab. Select the Hardware Ids, which will list het Vendor ID 197B and Device ID 2393.
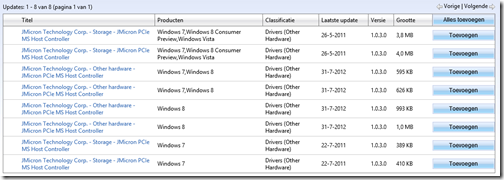
So, how can we find out what this device is, so that we can find a suitable driver for it. Well, actually Microsoft provides a website to look this information up. The website is called the Microsoft Update Catalogue. Before you can use the website you have to install an ActiveX control though, which means IE only. On the website you have a search field which you can use to input your Vendor ID and Device ID after which you hit search.
This results in the following page:
As you can see, this is a PCIe controller provided by a company JMicron. And you can now start searching for a suitable driver using several options.
- You can download the driver from Microsoft
- You can download the driver from HP, since my laptop is from HP this is an obvious place to search
- You can search on the Jmicron website, to see if I’m able to download a suitable driver
An article which can really help you to determine if the correct driver gets installed, is written by Mikael Nystrom aka the Deployment Bunny: Nice to know: – Why did Windows 7 pick THAT driver ?
Option C: Fully Successful
Well, if the installation is successful, and no performance or other issues arise you can use the machine. This scenario is a rare one though.
Step 3: Determine if the HW needs so called Driver Applications.
Some HW, especially laptops need to install some additional software in order to become fully functional. This software can be a utility in order to make some extra buttons work, but also some software which is needed in order to activate the 3G onboard modem.
Locate this software, and hope that the installer support unattended installation. See my blog post about Application installation best practices for more information on how to make this software available.
When successfully made available, add the software to the Task Sequence using the same WMI query you used to install the driver package to select the installation during execution of the task sequence on that HW model.
For updating the drivers:
Manufacturers update their drivers for several reasons, some reasons can be: bug fixing, performance improvements, added models in a family driver or necessary driver update to support backend feature among other reasons.
For maintaining we also have several options:
- If it isn’t broke don’t fix it
- Update on a regular basis.
Some HW manufacturers provide options to update drivers using utilities. If the driver is provided in an installer you can create an application, and deploy that application on a collection containing machines which have the old version of the driver which you want to update.

With the Dell systems, I am now only installing the system and network drivers. I have the Dell Client System Update installing in the as a task sequence so that it takes care of all the updates that are non-critical.