In the first part of this series I outlined what Microsoft changed in ConfigMgr 2012 in order to introduce Role Based Access Control. In the second part I outlined a possible scenario and started building the scenario up to the point where the OpCo roles will be mapped to the ConfigMgr roles, this post will discuss the steps taken.
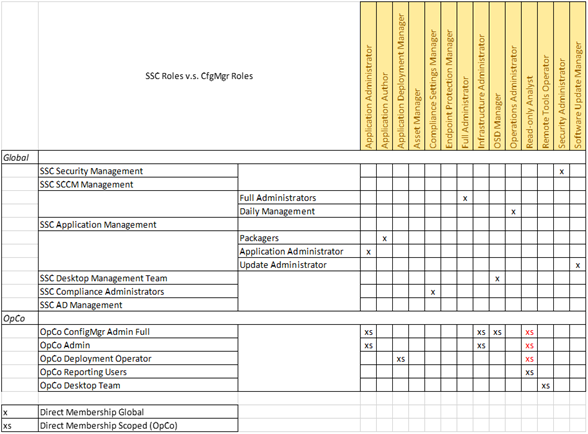
For the purpose of mapping the Customer roles to the ConfigMgr roles I created a spreadsheet to help out. Make sure that you understand what each OpCo needs to be able to do, and try to map this using the default roles. If not create a custom role and integrate this role into the matrix. My matrix turned out something like this:
Click below to download the Excel Sheet, which I use for mapping the Business roles to the Security roles within ConfigMgr.
A few remarks:
- We decided that the Full Administrators role, would only be given to a defined service account, for which the password would be made available when needed
- The SSC ConfigMgr Admins were given the Operations Administrator role
- The Read-Only analyst role is given to the OpCo ConfigMgr roles, for the reason that we are going to scope this Read-Only role to the SSC security scope. This means that they will have read-only access to objects that are scoped to SSC
Creating the roles within the ConfigMgr Console
The first thing we have to do is to create Security Groups within Active Directory, we are not going to authorize users directly (Full Administrators excepted), so we are going to use groups for that purpose. Once the groups are created we can create the roles. As an example I’m going to show you the Operations Adminstrator role within the SSC department and the OpCo ConfigMgr Admin Full role within OpCo1 and Desktop Team role within OpCo2.
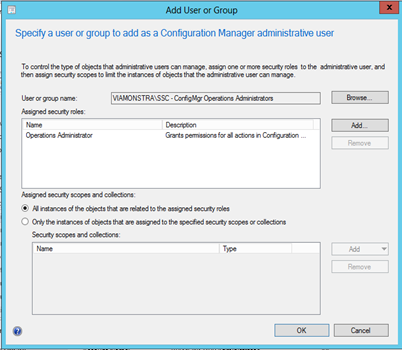
SSC Operations Administrator
Go to the Administration pane, and browse to the Security folder in order to select Administrative Users. Click on Add User or Group from the Ribbon.
Add the group name, in my case SSC – ConfigMgr Operations Administrators and assign the Operations Administrator security role. Make sure you select “All instances of the objects that are related to the assigned security roles” in order to make sure that this role can manage the whole hierarchy.
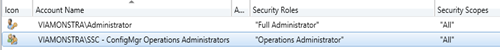
After creating the role, you will notice that this account is scoped to the “All” Security Scope, which means it will have access to all security scopes, even the scopes we create afterwards.
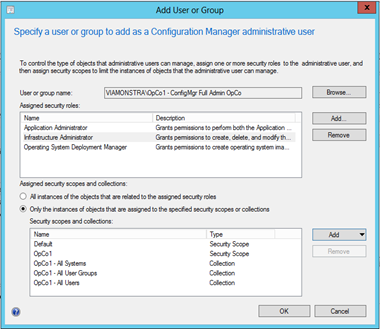
OpCo1 ConfigMgr Full Admin
Go to the Administration pane, and browse to the Security folder in order to select Administrative Users. Click on Add User or Group from the Ribbon.
Add the OpCo1 – ConfigMgr Full Admin OpCo group and give that group the following roles:
- Application Administrator
- Infrastructure Administrator
- Operating System Deployment Manager
Make sure that both the Default and the OpCo1 Security Scopes are added, we need to give access to the default security scope, because when a new object is created, like for example an Application, it gets the Default security scope. If we don’t give access to the Default Security Scope the User member of this group can create an Application (because he or she is Application Admin) but can’t see it after it’s created (because its scoped to default and not OpCo1)
After this role is created, we need to modify it a little bit, therefore we select the newly created role and click on Properties from the Ribbon.
Select the Security Roles tab and click on add to add the Read-Only Analyst role
Select the Security Scopes tab and select the radio button in front of: Associate assigned security roles with specific scopes and collections. As you can see all the ConfigMgr roles now have access to the same security scopes and Collections. Select the Read-Only Analyst Security Role and click Edit… Select everything and click remove, and only add the SSC Security Scope.
We now created the OpCo1 – ConfigMgr Fulle Admin OpCo role, which has the Application Administrator, Infrastructure Administrator and Operating System Deployment Manager role on security scope OpCo1 (and default), and who is Read-Only analyst on security scope SSC.
OpCo2 Desktop Team
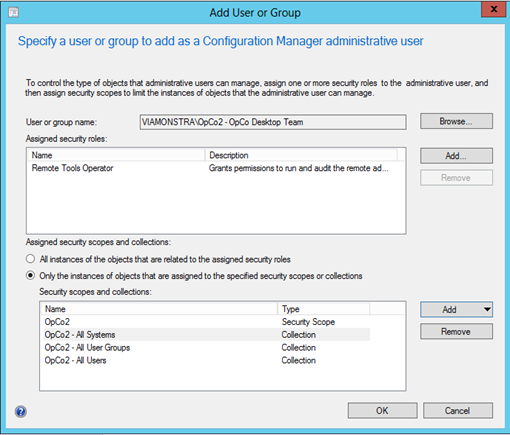
Go to the Administration pane, and browse to the Security folder in order to select Administrative Users. Click on Add User or Group from the Ribbon.
Give the group the Remote Tools Operator Security Role, and use the OpCo2 security scope and the OpCo2 – All Systems, OpCo2 – All Users and OpCo2 – All User Groups collections.
The desktop team doesn’t need the Read-Only operator role on the SSC scope, so for this role we can click OK for it to become active.
In this part of the series, we mapped the business roles to the ConfigMgr roles and created the roles in the ConfigMgr console. In the next part I’m going to show you the outcome and give some tips of the issues I encountered during implementation of this model.
All Articles in this serie:


Hi Kenneth,
Thank you for in-depth RBA understanding. Currently, I am trying to achieve something similar in our organisation. Bit of background information, we have CAS and Primary (P01). CAS resides in child domain and PR resides in parent domain. What we would like to do is, give full admin permissions to the Operations team full control of P01 but read only permission to CAS. we have created different scopes default and “P01”. We have assigned our Primary site to “PR” scope. For Ops team, under admin users we have assigned full admin rights to “P01” scope and read-only role to default scope. However, operations team is unable to access CAS in read-only mode.
Is there any way to achieve this ?
Thank you
Bav