The Microsoft 365 Apps admin center, available via https://config.office.com provides a portal where admins can manage Microsoft 365 Apps for Enterprise. Microsoft 365 Apps for enterprise is a subscription that comes with premium apps like Word, Excel, PowerPoint, Outlook, Teams, Publisher, and Access (Publisher and Access are only available on PC). The apps can be installed on multiple devices, including PCs, Macs, iPads, iPhones, Android tablets, and Android phones.
The Microsoft 365 Apps admin center used to be known as and sometimes still is referred to as the Office Customization tool or Office 365 Client Configuration Service. The Microsoft 365 Apps admin center contains the Office Cloud policy service, the Office customization tool and the Security policy advisor. Besides these functionalities there are also some features in preview worthwhile to implement in your organization.
Let’s have a closer look.
Office Cloud policy service
With the cloud policy service, you can create policies for Microsoft 365 Apps on devices. These policies contain many of the policy options you would normally have when creating a Group Policy Object (GPO) using an Group Policy Administrative Template. The devices you target can either be: Domain Joined, Azure AD joined but also standalone. The only requirement is that for the policies to apply the user needs to be signed-in. With the Office Cloud policy service you can also enforce some policies for Office on the web, either for signed-in or when used anonymously.
You can create a policy under Customization -> Policy Management in the Microsoft 365 Apps admin center. The same configuration is available in Microsoft Endpoint Manager under Apps -> Policies for Office Apps.
When creating a policy you must provide the name, optionally a description, provide whether the policy applies to users, or users that access documents anonymously using Office web apps, and select a group to which the policy will be applicable. Once provided, you can define the settings under “Configure policies”
This will bring up the available policies, which contains 106 pages with at time of writing a total of 2104 policies. You have the option to filter on Security baseline, giving you all the policies that Microsoft recommends in their security baseline, which narrows down the selection to 88 at the moment.
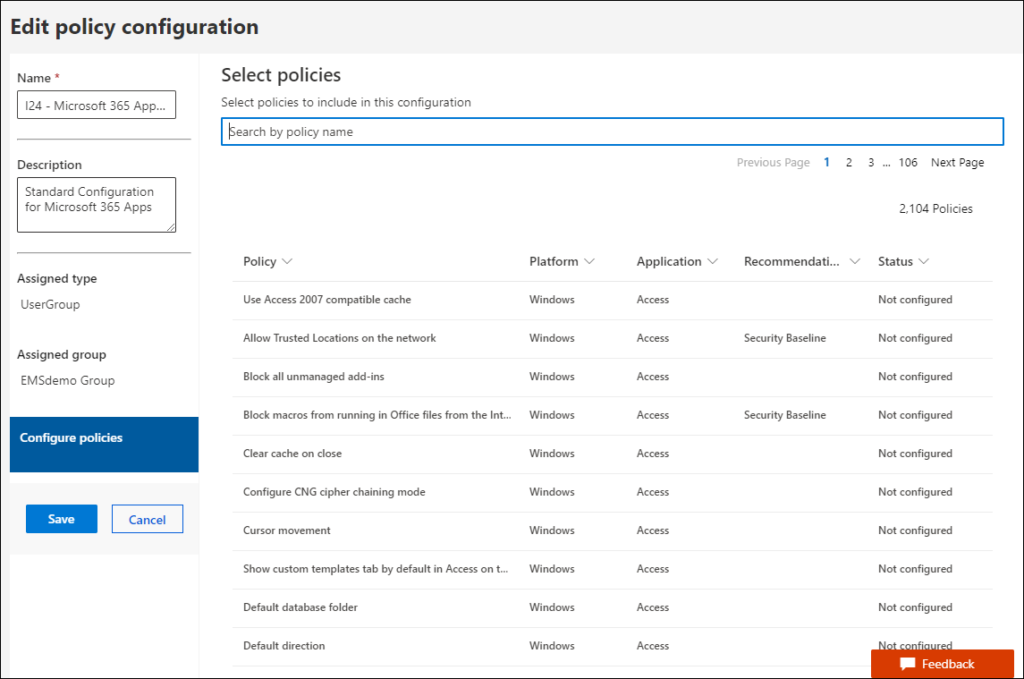
When filtering on platform you can either select Windows, Multiple and Office on the Web. Multiple means that the setting can also be applicable to MacOS, iOS and Android. Especially iOS and Android are interesting here, since we also have App Configuration Policies in MEM to configure App behavior here.
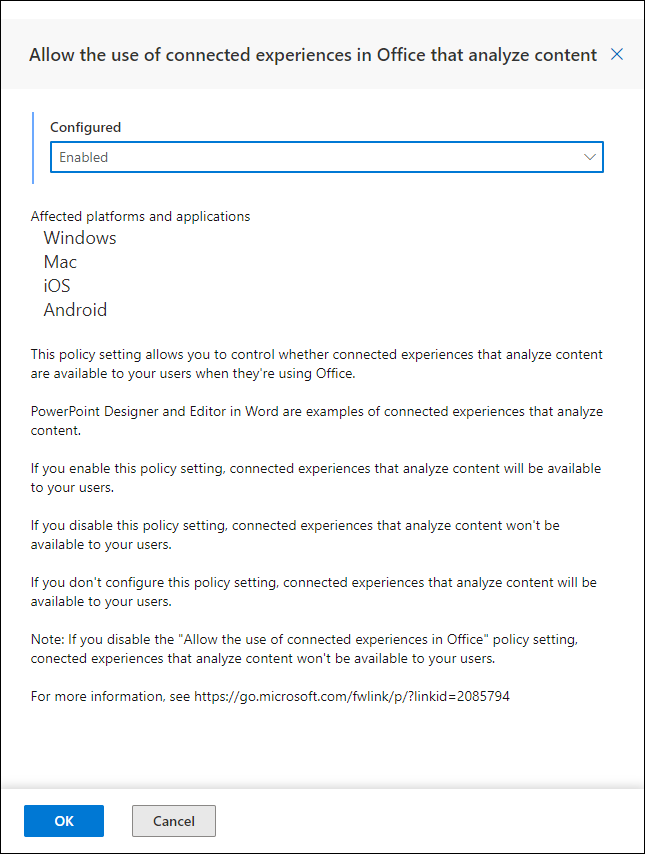
Each setting, when clicked opens up a new windows giving you much detail on what the settings does, for which platform its applicable and of course how you want to configure it.
Once the policy, or policies are created you have the option to copy the policy, set the priority (allowing you to define which policy wins if multiple are applicable to a user). What’s also really interesting is the Recommendation status, because after you create the policy you might receive the message that New recommendations are available.
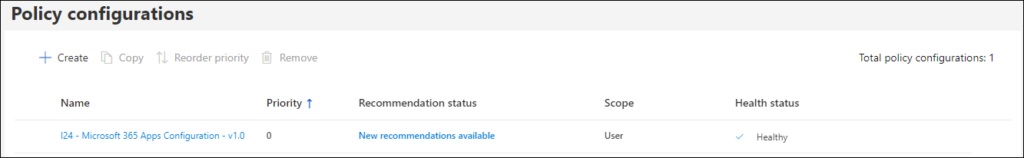
Clicking on the New recommendations available link will open the security policy advisor.
Security policy advisor
You can use Security Policy Advisor to receive and implement security policy recommendations. These recommendations are based on Microsoft best practices and information about your existing environment.
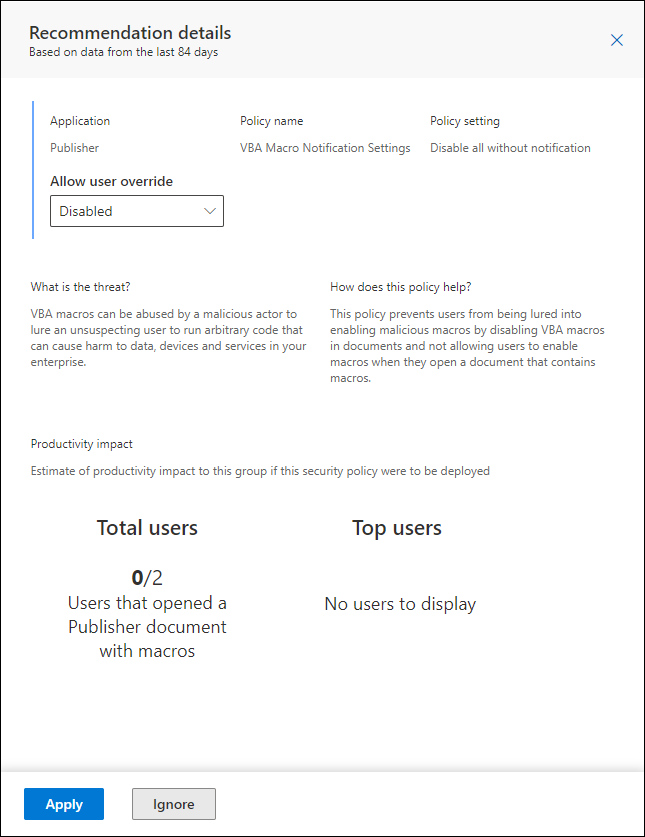
The Security policy advisor gives recommendations for your created policies. Using a selection button you can either select or deselect any recommendations which might have a high productivity impact. As you can also see, based on inventory within your organization, the advisor shows who are impacted if you change the setting. If you select the setting, you can choose to either Apply the setting or to Ignore it. You can view the settings you applied on the “Applied policies” tab. Each setting must be applied individually which can be time consuming.
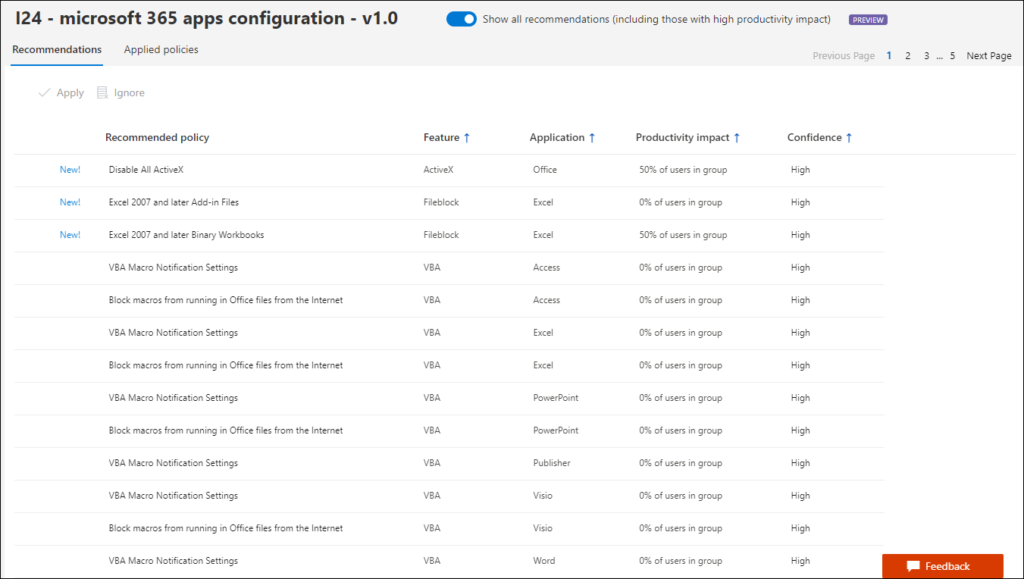
If you select a specific setting a new Window will be opened giving you more detail about the specific setting. Here you can also define whether the user is allowed to override the setting, so that you can distinct between a forced setting, or a default you want to apply initially.
Office customization tool
The online Office customization tool provides a nice interface allowing you to create Office configuration files (configuration.xml). With Office 365 configuration files you can influence the installation of Office and define how Office will be installed. You can define which applications and languages are installed, how those applications should be updated, and application preferences.
The configuration files can either be used in combination with the Office Deployment Tool, and be used by, for example Microsoft Endpoint Configuration Manager (ConfigMgr), or Microsoft Endpoint Manager (Intune).
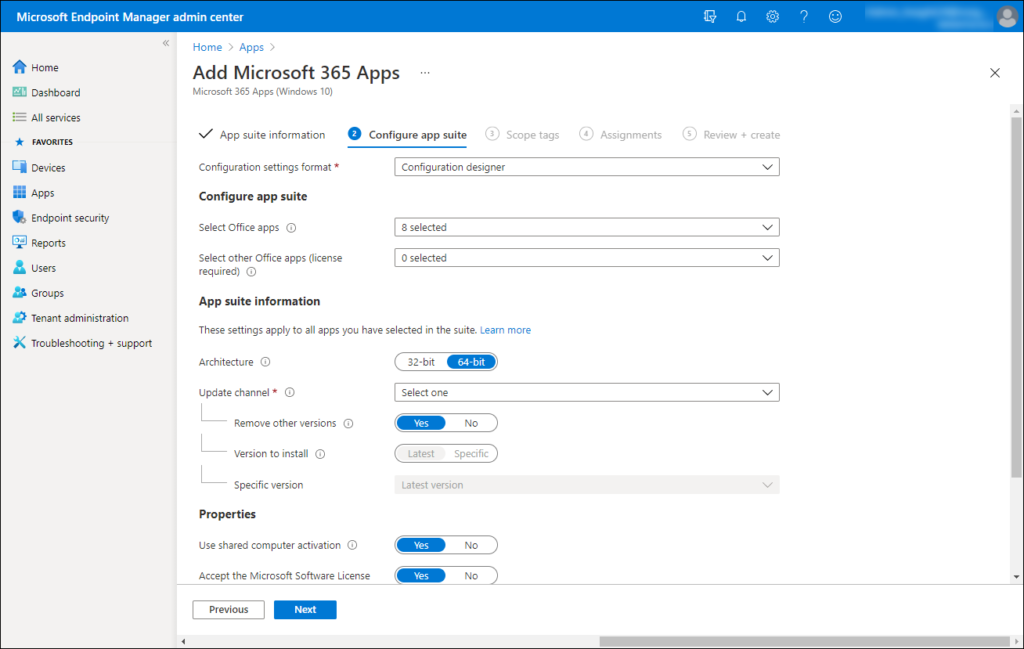
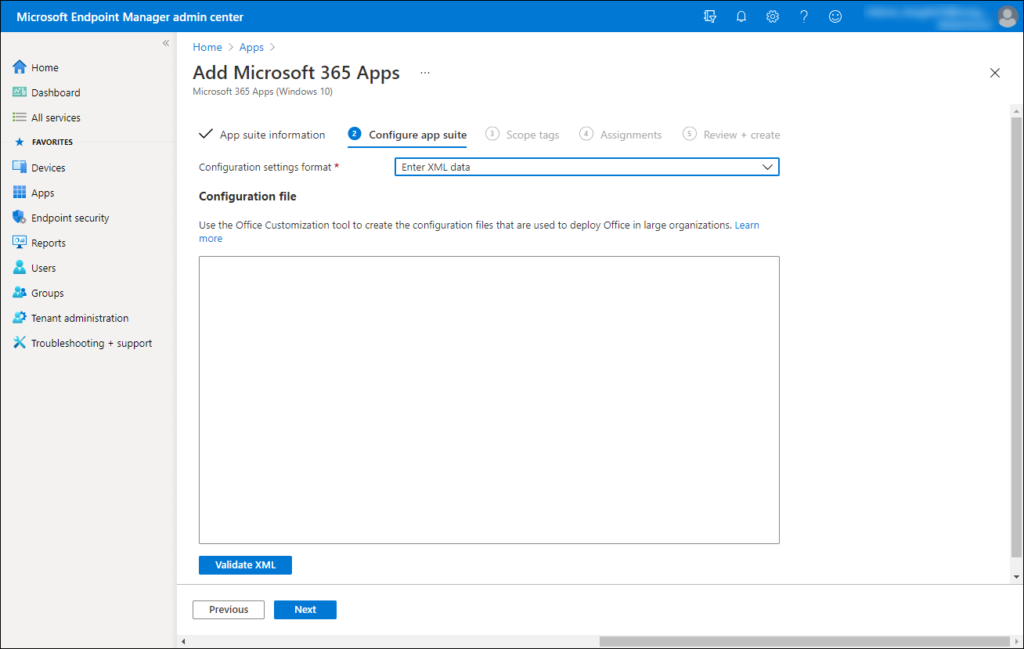
In Microsoft Endpoint Manager as an example, while creating the Microsoft 365 Apps installation definition, you have two options. You can either use the Configuration designer, which gives you some basic options to configure like the Apps to install, and specifying the architecture. You can also select to Enter XML data directly, allowing you to use the full options provided by the Office Customization Tool.
Creating Office customization configurations in the Apps Admin center
The Office Customization Tool can be found under another name in the portal and is available under Customization -> Device Configuration.
The Device Configuration section has several tabs:
My Configuration
Allows you to create, import and store your own configurations, with a maximum of 100. I haven’t tried if this maximum is enforced.
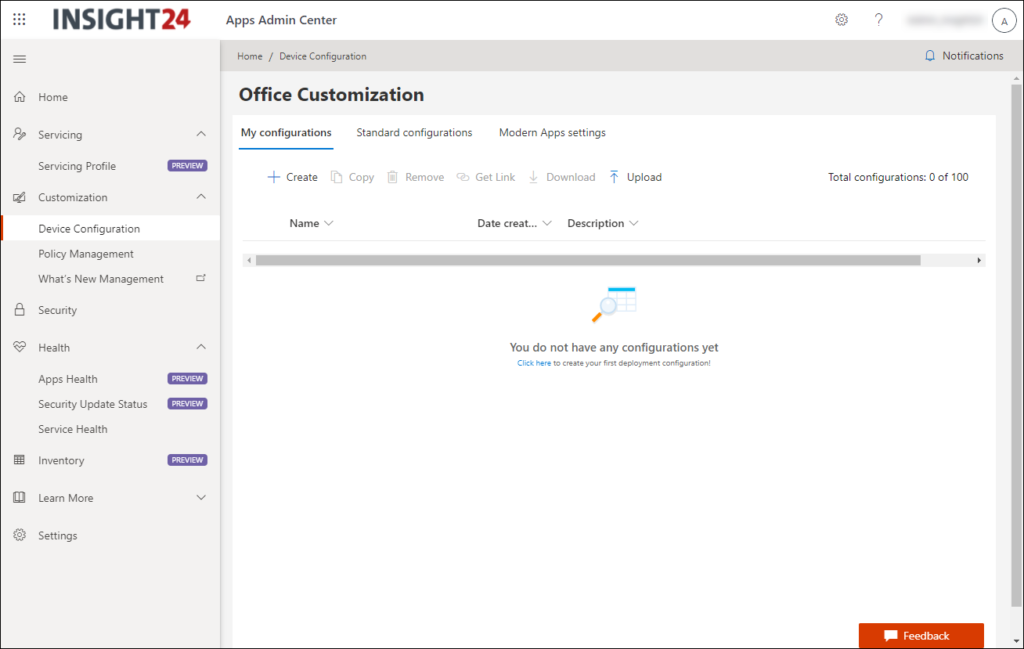
From here you can create a new configuration from scratch. If you click on “+ Create” the Office Customization Tool will open. I will not go into details about which options you must use in order to create a Config file, if you want to know more, please visit the following page: Create a configuration file.
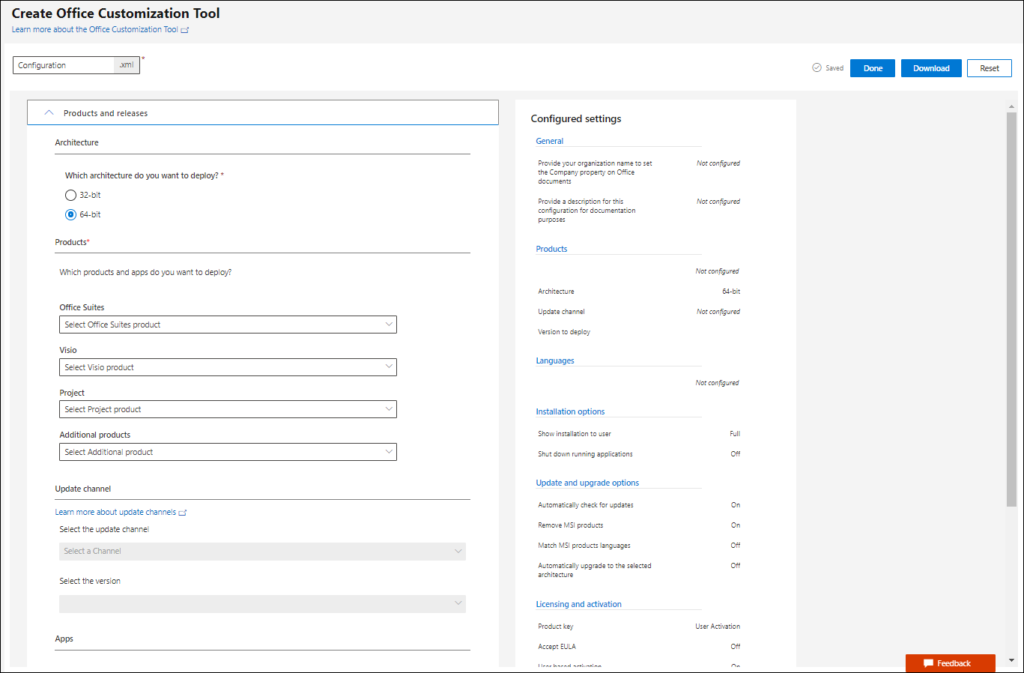
It’s important that you make sure that while configuring your own custom configuration file, that you address all the fields which are mandatory. If you don’t, you cannot download the file and probably miss some must have information while deploying.
You also have the option to copy an existing configuration file and work from there, import an configuration file and bring it into the environment. Another interesting option is to get a link to the file, which you can use while running the Office Deployment Tool. You can use the /configure “link” option to call the link directly from the tool.
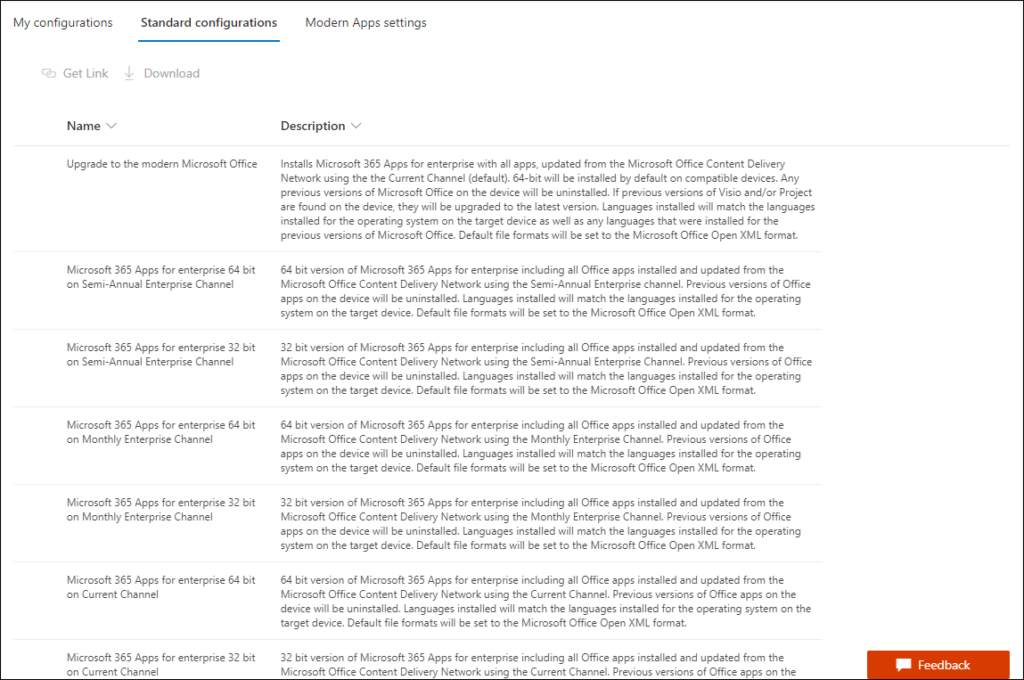
Standard configurations
The Standard configurations tab provides templates which you can use to deploy the Microsoft 365 Apps. Microsoft created some scenario’s which you can use. From here you can either create a link to the template and use it in the Office Deployment Tool, or you can download the configuration file. If you want to modify one of the templates you must download the file first, and upload it again under My configurations. (for now)
Modern Apps settings
Modern Apps settings currently allows you to select whether the Microsoft Edge WebView 2 rendering engine will be installed. Microsoft 365 Apps is starting to provide new or improved features that rely on Microsoft Edge WebView2. For example, the Room Finder and the Meeting Insights features in Outlook. WebView2 uses Microsoft Edge as a rendering engine to display web-based features in a desktop application.
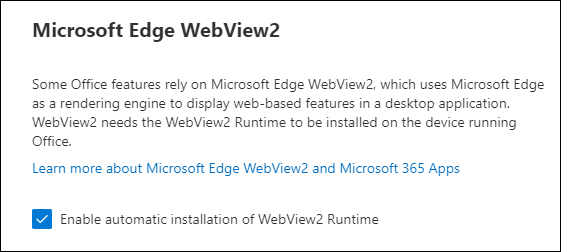
I expect other options to show up here also in the future.
Other options
Besides the Office Cloud policy service, the Office customization tool and the Security policy advisor the Microsoft 365 Apps portal contains some other options as well.
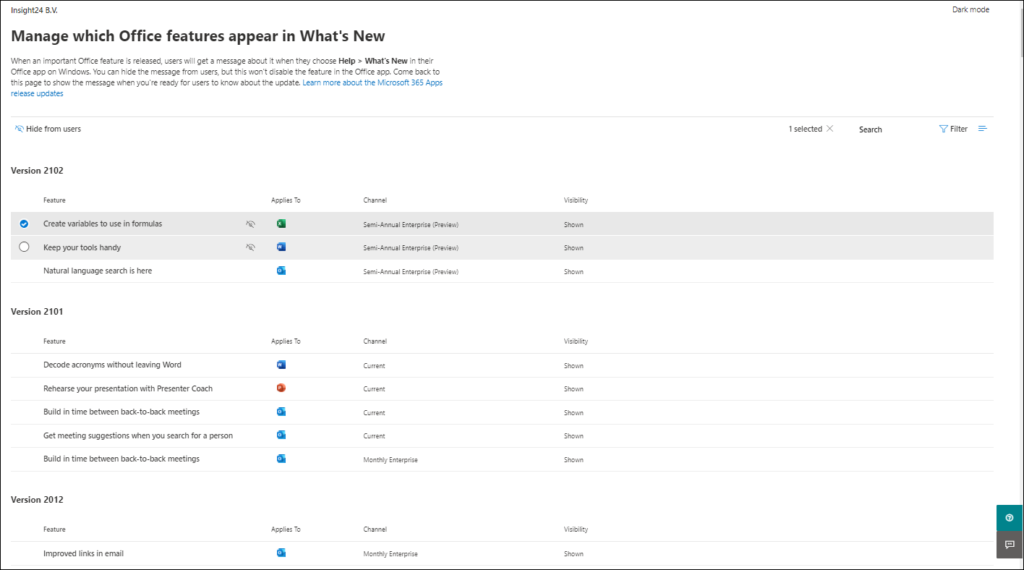
What’s new management
What’s new management, which can be found under customization when clicked opens up a new windows to the Microsoft 365 admin center, where you’ll end up in the “Which Office features appear in What’s New” configuration page. You would normally find this page under Settings -> Org Settings -> What’s new in Office in the Microsoft 365 admin center.
When an important Office feature is released, users will get a message about it when they choose Help > What’s New in their Office app on Windows. You can hide the message from users, but this won’t disable the feature in the Office app.
Preview features
At time of writing the following services were available in preview. If you want to start using these preview features you must enable them and accept the license terms first.
Once enabled you might have to wait a while, for data to be provisioned
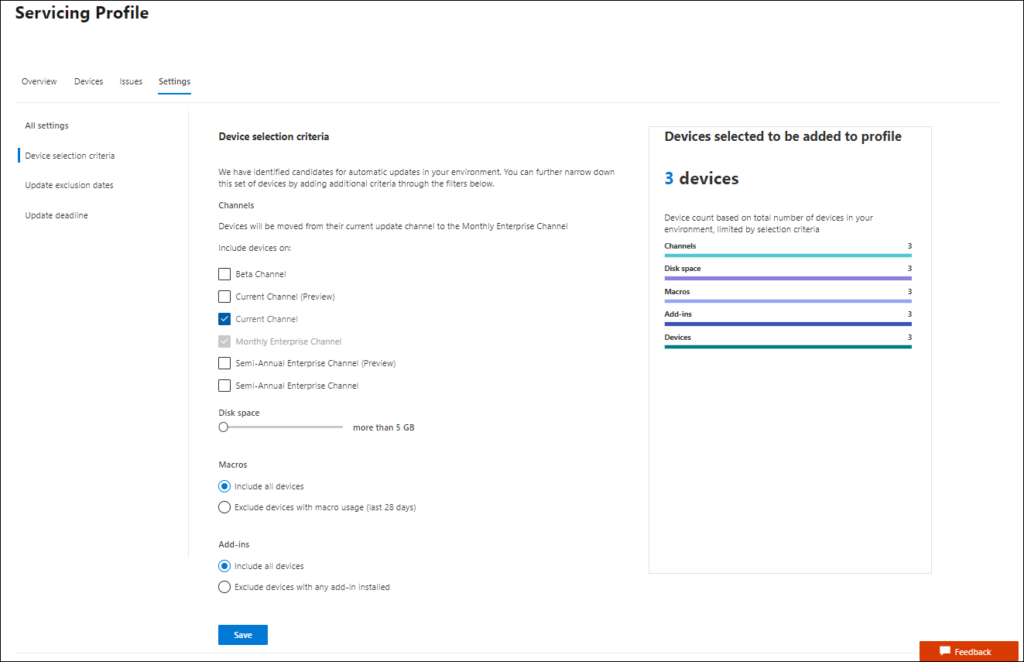
Servicing Profiles
With servicing profiles, you can automatically deliver monthly Office updates for specific users or groups. You can only use this if you have Microsoft 365 Apps for enterprise, Version 2007 or later or Microsoft 365 (or Office 365) A3, A5, E3, or E5 subscription plan. You must also have a Windows 10 version supported by Microsoft 365 Apps for Enterprise. (so LTSC will probably not be supported here)
You can apply a servicing profile to a set of devices in the Microsoft 365 Apps admin center. When you apply the profile, the following changes occur:
- The devices are moved to the Monthly Enterprise Channel
- Updates to the device come from the Office Content Delivery Network (CDN)
- The devices are managed by the servicing profile
Devices in the servicing profile receive updates for the Monthly Enterprise Channel beginning the second Tuesday of every month. Updates are delivered in waves to limit the impact on the network. You can pause updates and investigate and resolve update issues. You can also set deadlines for updates to be installed and dates on which updates cannot be installed.
Apps Health
Apps Health provides a set dashboards which monitors reliability and performance metrics and provides custom guidance to help optimize and troubleshoot Microsoft 365 Apps on your client devices. The Apps health dashboards provided are:
Overview
App Metrics, giving you an overview on how many sessions of an app have been recorded. For each app you can dive in deeper and select metrics like App session crash rate, App boot time and others.
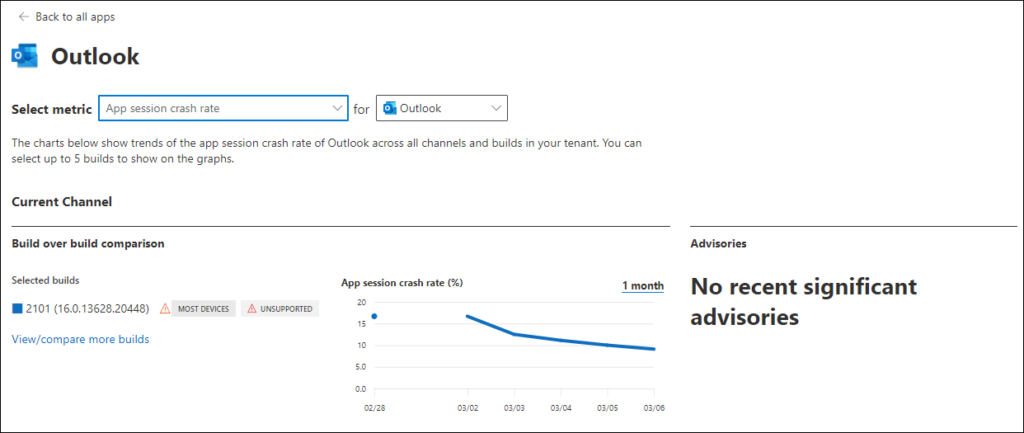
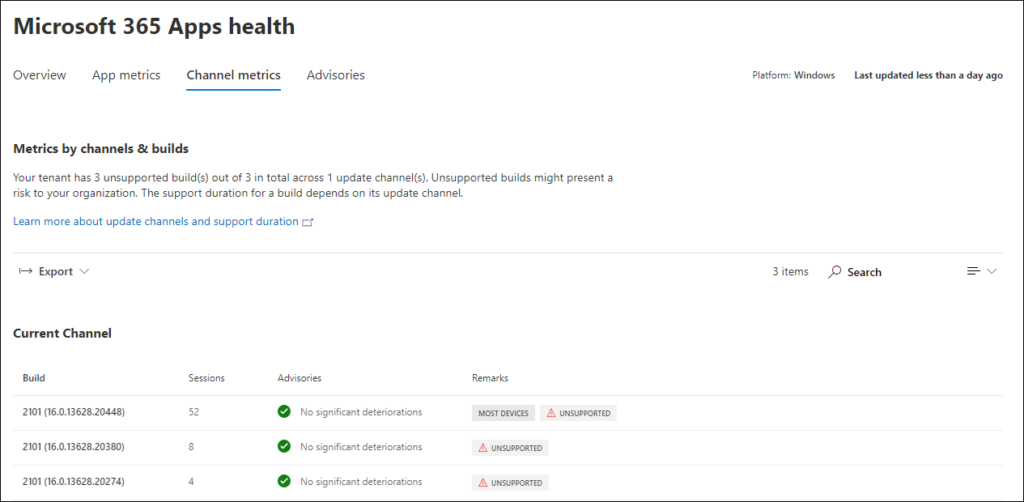
Channel Metrics
Gives you a similar overview but then based on build versions. For each build you can dive in deeper and show more detail. Interesting in this case is that probably within my tenant I have unsupported builds detected, while we do run the latest versions. (something to look into, or maybe something to be fixed in the solution)
Advisories
Shows the latest advisories on performance and reliability regressions in occurring on your tenant. You can select any advisory to see advisory details.
The advisory view will help you understand the context of the regression and get guidance. On this view, you will see:
- Office client, build, and metric where a regression has occurred
- Number of user sessions in the impacted build and app
- Value of the monitored metric when the regression was detected
- Current value of the monitored metric
- Recommended troubleshooting actions
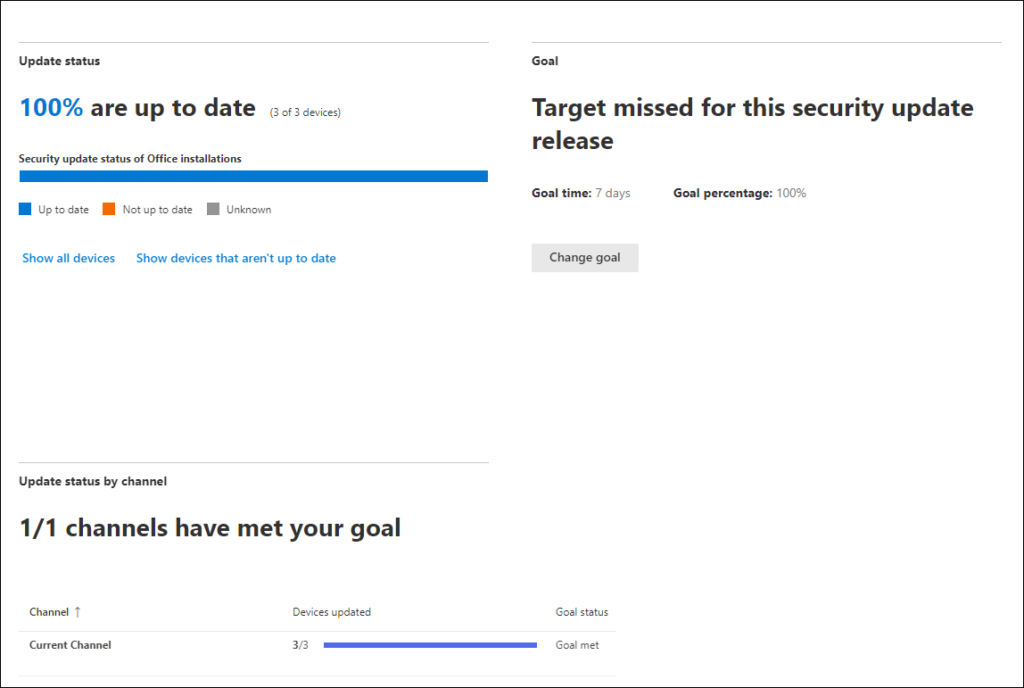
Security Update Status
On the Security Update Status page you can see which devices have installed the latest security updates for Office. The status can either be:
- Up to date – Device that has installed the latest security patch
- Not up to date – Device that has not installed the most recent security update
- Unknown – Status of the security update could not be retrieved.
From here you can also specify a Goal, in the example below to have all devices up to date within 7 days. You can specify the percentage of devices you want to update and the schedule for meeting that target. This doesn’t create any policies or changes to your devices. It is used only for reporting on the security update status page.
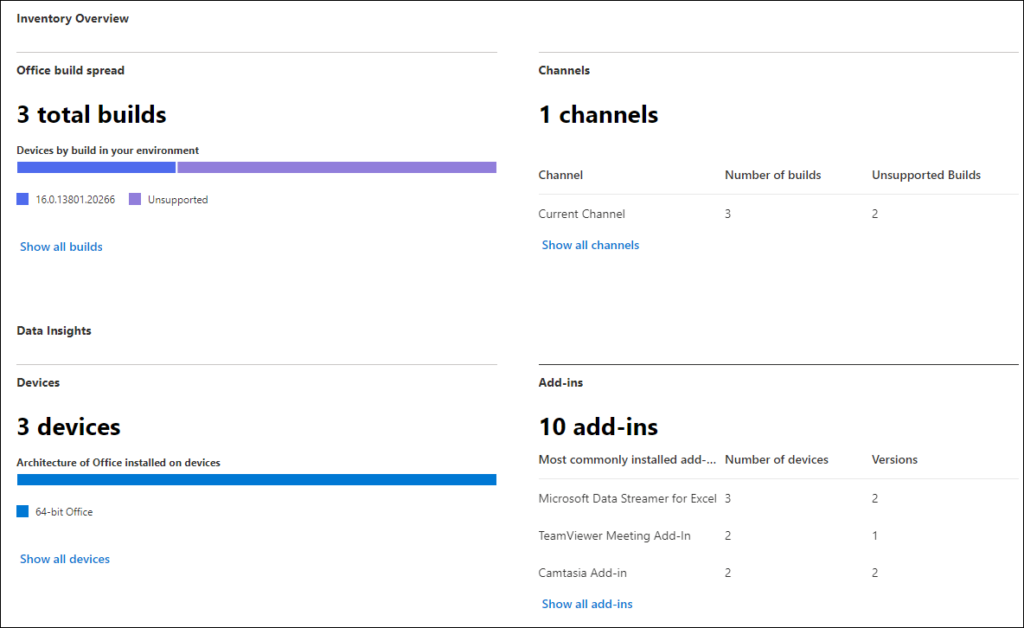
Inventory
The Inventory section allows you to see information about the devices in your organization, including hardware, operating system, and the Office software running on that device. The following information is displayed:
- Number of different Office builds
- Number of different Office update channels
- Number of devices which Microsoft 365 Apps, version 2008 or greater, are installed.
- Top installed add-ins on those devices.
Conclusion
The Microsoft 365 Apps admin center is yet another Administrator portal in the portfolio of products coming from Microsoft. If you want an overview of all portals available check out: https://msportals.io/.
If you are managing Microsoft 365 apps in your environment, this portal does provide additional value. So my advice would be to have a look yourself and start using its functionality. It’s clear though that the portal is still a work in progress as some functionality is not smooth yet which results in bad scaling for example, and preview features are being added.
Let’s hope that Microsoft continues to extend the functionality, but most important keeps the possibilities consistent with other available tooling. Take for example the option to define settings for iOS and Android apps, it would be very annoying to have settings coming from an App Configuration Profile (set using MAM in MEM) conflicting with settings coming from the policy service. That would be really nasty to find if these issues occur. There is some available consistency available, as an example the fact that the Policies for Office apps option in MEM refers directly to the same settings in the Apps admin center.
It would really be nice if somehow also App Protection Policies and App Configuration Policies would merge into this solution as well, ideally I would like to see that the Office Desktop App on both Windows and MacOS will become fully MAM capable, just as the App versions on iOS/Android are. With additional support for Conditional Access (Require approved app/app protection policy) we can then support Office usage on non-managed (not-compliant) devices.
References
Overview of the Office cloud policy service for Microsoft 365 Apps for enterprise
Overview of Security Policy Advisor for Microsoft 365 Apps for enterprise
Overview of the Office Customization Tool
Overview of inventory in the Microsoft 365 Apps admin center
Overview of the security update status report in the Microsoft 365 Apps admin center
Overview of servicing profile in the Microsoft 365 Apps admin center
Can you help clarify? The Office policies have an “Assigned type” of UserGroup. You write that devices can “Domain Joined, Azure AD joined but also standalone”, but isn’t that irrelevant, since they can’t be targeted?
Thanks!