In February this year I blogged about Stopping automatic email forwarding in your Exchange Online environment in a controlled way providing a structural way to disable automatic email forwarding within your organization, while still allowing exceptions.
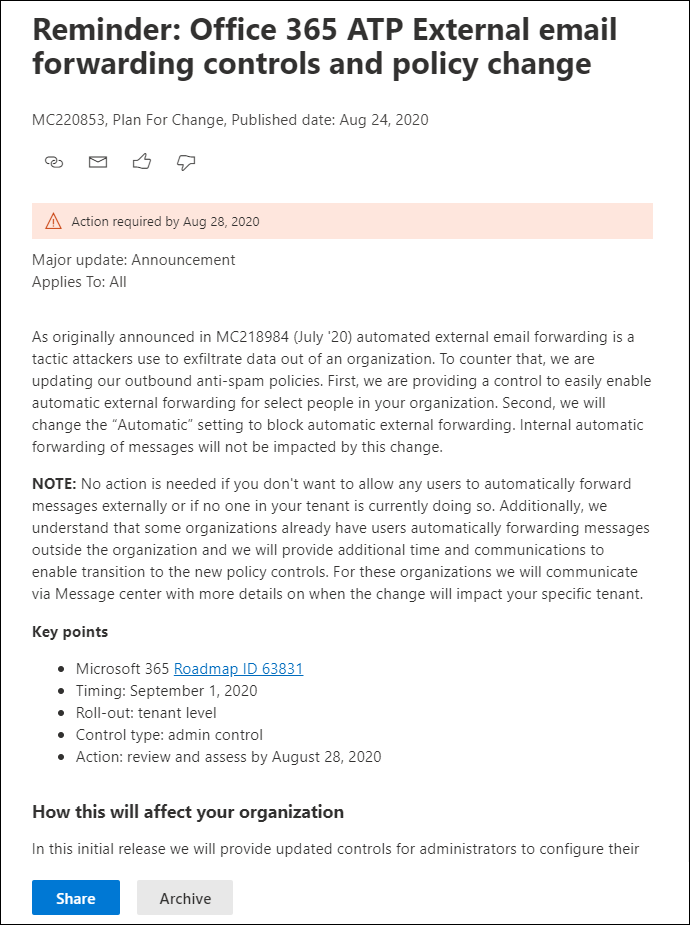
This week Microsoft announced through the message center (MC220853) they are rolling out the External Email Forwarding Controls functionality for customers with Office 365 Advanced Threat Protection (ATP) licensed.
Update October 30, 2020: Microsoft has now communicated the following in the message center (for my tenant): As a follow up to MC221113 (August 28th), on September 1st, 2020 the Auto-Forwarding Policy will be enforced for tenants who have configured their policy to “On” or “Off”, this includes tenants that had users external forwarding prior to September 1st 2020.
Your tenant has been identified as having existing users using external forwarding prior to September 1st 2020, and for this reason the “Automatic” setting will default to “on”, i.e. external forwarding is allowed. We will contact you through a separate message center post when the “Automatic” setting will be updated to “off”.
Update August 31, 2020: Microsoft has now communicated the following in the message center: For organizations that have some users externally forwarding prior to September 1st 2020 the setting “Automatic” will default to “On” and we will contact you separately when this will change for your tenant.
From the roadmap – Office 365 ATP: External Email Forwarding Controls
External forwarding of email is a tactic used by attackers to exfiltrate data out of an organization and controlling that process is difficult. With this new feature we are adding support for more granular controls that allow the Office 365 administrators to easily enable external forwarding for the right people in the organization through the outbound spam policy. We are also moving to disable external forwarding by default so organizations are secure by default.
Am I impacted?
You are impacted if you have licensed ATP functionality and are using the default Outbound Spam policy or any other outbound policy.
Note: The above statement is for sure, for non ATP licensed tenants I do see the option in the Outbound Spam Policy, but I’m not sure if these tenants are impacted once Microsoft flips the switch. Communication mentions that this is an ATP functionality, but in that case the forwarding option shouldn’t be available in the Outbound Spam filter policy for non ATP tenants. So be aware!
The message center message notes the following:
No action is needed if you don’t want to allow any users to automatically forward messages externally or if no one in your tenant is currently doing so. Additionally, we understand that some organizations already have users automatically forwarding messages outside the organization and we will provide additional time and communications to enable transition to the new policy controls. For these organizations we will communicate via Message center with more details on when the change will impact your specific tenant.
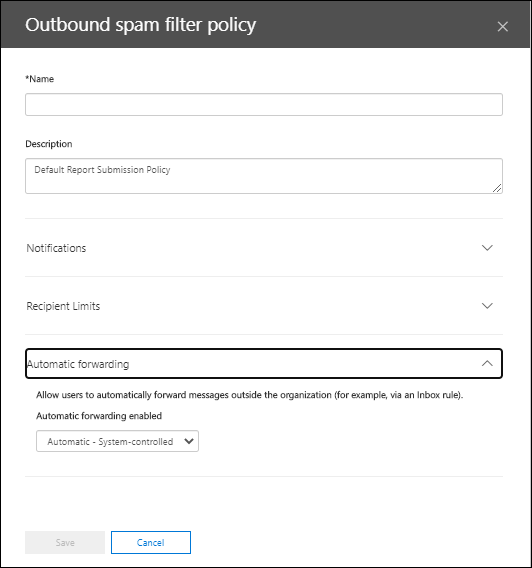
As you can see in the screenshot below, the default setting is “Automatic – System controlled” for which Microsoft just announced that this option will disable automatic email forwarding starting September 1st (within one week at time of writing)
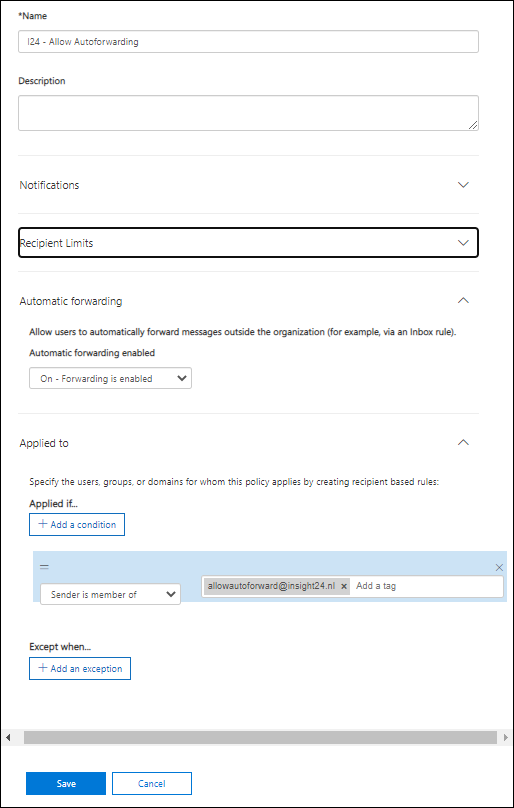
How to mitigate?
You can make sure that your exception list (as mentioned in my other article on this subject) is still allowed to automatically forward, create a new Outbound Anti-Spam policy, enable automatic forwarding and scope this to your allow group.
Conclusion
Even though I fully support having automatic email forwarding disabled by default, this is a change which can have some impact on customers currently having some legit scenario’s which allow for automatic forwarding.
Make sure that you are ready when Microsoft implements this change, the way I read it they will flip the switch on September 1. Make sure you have taken countermeasures if you want your exceptions to keep working.
For non-ATP customers – I’m not sure if you are impacted since the option is available in non-ATP tenants as well – verify the impact of this change on September 1 if you want to be sure.
8 thoughts on “Microsoft is making changes related to automatic email forwarding for ATP customers, here is what you need to know”