I’m a big fan of integrating the Microsoft Deployment Toolkit into ConfigMgr, but notice that I’m having a hard time to convince my customers (and some fellow Deployment enthusiasts) of the added value. Personally I think that has something to do with the overwhelming added functionality you get. Take for example the MDT created Task Sequence, which looks very complex in the beginning, but once you get the know the MDT generated Task Sequence you will begin to see its added value. I firmly believe that you can have one task sequence per OS type, and from that Task Sequence you can install several configurations.
Ok, so what’s the goal in these series of blogposts.
This post will detail how you can use standard functionality provided in a MDT task sequence, to write some registry values based on variable settings which we can later use to determine under what circumstances a machine was deployed. We are going to modify our MDT Task Sequence in order to enable branding when not using User Driven Installation (UDI), define some custom variables to use and later use Configuration Items, and Configuration Baselines to create Collections based on this information which branded in the registry of clients.
So let’s start.
First you will have to create an MDT generated task sequence.
- Install MDT on the machine where you run your ConfigMgr console
- Run the MDT integration wizard so that the functionality provided by MDT is added to the ConfigMgr console
- Now, go to the Software Library and go to the Operating Systems node and select Task Sequences
- You will notice that in the Ribbon you now see a Create MDT Task Sequence button
- When you click on the Create MDT Task Sequence you will start the Create MDT Task Sequence wizard which will guide you to creating a MDT generated task sequence.
The MDT Task Sequence Wizard, can automatically create some of the needed packages, like the User State Migration Tool (USMT),MDT Files Package and the MDT Settings Package (containing the customsettings.ini)
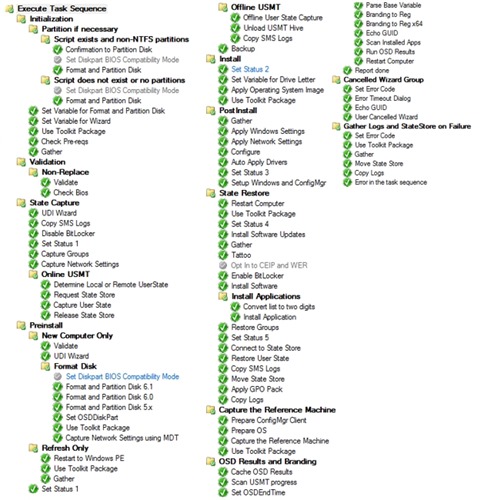
When the wizard is finished and the new Task Sequence is created you can open the Task Sequence, and the result can be very overwhelming, see below. What you see though, is a task sequence which contains support for all OSD scenario’s, support for central logging, support for user data migration (USMT) and many other features which are provided as added value due to the MDT integration.
One of the features we are going to use in this blogpost is the Branding to Reg functionality. As you can see this step (actually two) is part of the OSD Results and Branding section, which only runs when User Driven Installation (UDI) Wizard is used.
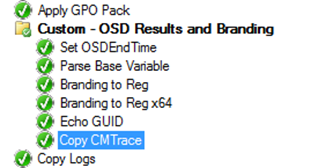
So if we want to use the Branding functionality in a Task Sequence where UDI is not used, we need to copy the Set OSDEndtime, Parse Base Variable, Branding to Reg and Branding to Reg x64 steps to a place which is run in a ZTI task sequence. In case of the task sequence above, I suggest to add these three steps between Apply GPO Pack and Copy Logs in the State Restore phase. When I modify my MDT generated task sequence, I always name the modified step, or sequence of steps Custom – <name of step> – this allows me to see what is modified compared to the default easily.
After these steps are added and you run your Task Sequence you will notice that after installation a new Registry key is added to your deployed machine. You can find this registry key under HKLM\Software\Microsoft\MPSD\OSD.
In part 2 of these series, we are going to extend the OSDBranding functionality so that some extra useful information is written to the above registry location as well.
Is there a reason for having to use both “Branding to Reg” and “Branding to Reg x64” in a single Task Sequence? The only real difference I can see is that each one writes the TS variables to 2 different locations in the registry. What would the impacts be for removing one versus the other? I am currently using SCCM 2012 SP1 with MDT 2012 U1 and UDI btw.
Hi David,
Thanks for your comment:
I just copied the steps from the MDT generated task sequence. I think both steps are still necessary if you want to execute the task sequence on both 32-bit and 64-bit systems.
/Kenneth
I am new to Sccm deployment. I would to implement your task sequence into my lab
Can you add two more things into your task sequence.
1 credential check (only domain admin can initialize task)
2 option to select organisation unit
Could you please send me your task sequence with all the script. @ thrqureshi@gmail.com
Thanks