Today, after installing a fresh System Center 2012 Configuration Manager Service Pack 1 environment, we experienced that the Boot images for both 32- and 64-bit were not created. The reason for this is already widely known, because it had to do with the virus scanner which was active at time of installation. There are already some articles describing what can go wrong during an upgrade to Service Pack 1 for example, as described in the following article: Updated System Center 2012 Configuration Manager Antivirus Exclusions with more details on OSD and Boot Images, etc… . So lesson one here: Please disable the virus scanner during installation and make sure the correct exclusions are in place after installing the ConfigMgr environment.
So, we ended up with a running ConfigMgr 2012 SP1 environment without Boot images. So I was challenged to come up with a solution. As you may or may not know you can’t simple import the boot.wim from the Windows ADK installation and import it. This was already partially described by Kenny Buntix in the case of where the boot images weren’t updated after the upgrade to Service Pack 1. You can read more about that here: “CM2012 SP1 – No default boot images available / “Only finalized boot images are supported“”. My challenge though was a little bit different, because I had no boot images at all, so updating them wasn’t an option, because there was nothing to update.
Fortunately I found an article by Microsoft on how to create the boot images for use in System Center Configuration Manager 2007, titled: “How to Add a Boot Image to Configuration Manager” and adopted the steps for use with ConfigMgr 2012 Service Pack 1, as described below.
Steps Summary:
- Copy for both x86 and x64 the winpe.wim from the ADK to a temporary location
- Mount the boot image and apply four optional components to your mounted image using Dism:
- WinPE-Scripting
- WinPE-WMI
- WinPE-SecureStartup
- WinPE-WDS-Tools
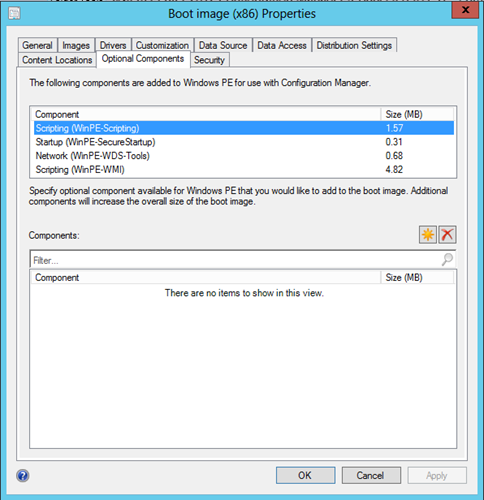
For more information about the optional components which you can add to Windows PE see: Windows PE Optional Components Reference. Keep in mind though that once imported into ConfigMgr, you can add these using the Optional Components tab on the properties of the Boot Image.
- Unmount the boot image and commit it
- Import the newly created boot image into ConfigMgr 2012
Detailed Steps:
- Create a temporary folder for storing the winpe.wim from the ADK, mine were in c:\temp\x86 and c:\temp\x64. I also already renamed the winpe.wim to boot.wim, and i created the c:\temp\mount folder to which i mount the wim file later.
Steps for the 32-bit Boot Image are described:
- Open the Deployment Tools Command Prompt as an Administrator
- dism.exe /mount-wim /wimFile:c:\temp\x86\boot.wim /index:1 /mountdir:c:\temp\mount
Deployment Image Servicing and Management tool
Version: 6.2.9200.16384
Mounting image
[==========================100.0%==========================]
The operation completed successfully.
- Install the necessary components in the boot image. In order to find out which optional components needed to be installed, I checked my private ConfigMgr 2012 installation running on my laptop. Also keep in mind that if you run McAfee AV, you must disable the AV while using this procedure, as acknowledeged by McAfee here: DISM.exe generates an Error: 5 or Access Denied when VSE 8.8 Access Protection is enabled
- Run: dism.exe /image:c:\temp\mount /add-package /packagepath:”D:\Program Files (x86)\Windows Kits\8.0\Assessment and Deployment Kit\Windows Preinstallation Environment\x86\WinPE_OCs\WinPE-Scripting.cab”
Deployment Image Servicing and Management tool
Version: 6.2.9200.16384
Image Version: 6.2.9200.16384
Processing 1 of 1 – Adding package WinPE-Scripting-Package~31bf3856ad364e35~x86~
~6.2.9200.16384
[==========================100.0%==========================]
The operation completed successfully.
- Run: dism.exe /image:c:\temp\mount /add-package /packagepath:”D:\Program Files (x86)\Windows Kits\8.0\Assessment and Deployment Kit\Windows Preinstallation Environment\x86\WinPE_OCs\WinPE-WMI.cab.cab”
Deployment Image Servicing and Management tool
Version: 6.2.9200.16384
Image Version: 6.2.9200.16384
Processing 1 of 1 – Adding package WinPE-WMI-Package~31bf3856ad364e35~x86~~6.2.9
200.16384
[==========================100.0%==========================]
The operation completed successfully.
- Run: dism.exe /image:c:\temp\mount /add-package /packagepath:”D:\Program Files (x86)\Windows Kits\8.0\Assessment and Deployment Kit\Windows Preinstallation Environment\x86\WinPE_OCs\WinPE-SecureStartup.cab”
Deployment Image Servicing and Management tool
Version: 6.2.9200.16384
Image Version: 6.2.9200.16384
Processing 1 of 1 – Adding package WinPE-SecureStartup-Package~31bf3856ad364e35~
x86~~6.2.9200.16384
[==========================100.0%==========================]
The operation completed successfully.
- Run: dism.exe /image:c:\temp\mount /add-package /packagepath:”D:\Program Files (x86)\Windows Kits\8.0\Assessment and Deployment Kit\Windows Preinstallation Environment\x86\WinPE_OCs\WinPE-WDS-Tools.cab”
Deployment Image Servicing and Management tool
Version: 6.2.9200.16384
Image Version: 6.2.9200.16384
Processing 1 of 1 – Adding package WinPE-WDS-Tools-Package~31bf3856ad364e35~x86~
~6.2.9200.16384
[==========================100.0%==========================]
The operation completed successfully.
Keep in mind that my ADK was installed on the D: drive, you should modify this to C: if you used the default installation path.
- We now unmount the WIM file and commit the changes: dism.exe /unmount-wim /mountdir:c:\temp\mount /commit
- Repeat these steps for the 64-bit boot image
Both Images are now ready to be imported into ConfigMgr 2012, add them to the default folder for ConfigMgr <%configmgr install folder>\OSD\boot\%architecture%>and import them from the default \\%siteserver\sms_%sitecode% share.
Note: Since CU2 we can now also import boot images from the WAIK again, for reasons known. Even though the functionality you have on these kind of images is limited, the procedure to import them is similar to what’s described above. See this article for more information: How to Create and Import a WinPE 3.1 Boot image for use in ConfigMgr 2012 SP1 CU2
Awesome to say the least!!!
This has helped me 100%
Thank you for such a thorough explanation. And very well documented,