TL;DR; – When reinstalling Windows on a Surface Pro 6 and it fails, make sure that you “temporarely” disable the ” Enable boot configuration lock” option and try again.
At one of my customers we are using MDT to install Surface Pro 6 devices in order to make sure that the latest version of Windows 10 is available when starting the Out of the Box Experience (OOBE).
While testing this solution, we experienced some machines starting to fail to install Windows 10, where MDT would exit with the following error code: Litetouch deployment failed, Return Code = -2147467259 0x80004005
Time for a deepdive:
Within MDT, the LTIApply.wsf script is responsible for applying the WIM image to the system, the logging (LTIApply.log) stated the following:
The image D:\Deploy\Operating Systems\REFW10-001_10-2-2019\REFW10-001_10-2-2019.wim was applied successfully. LTIApply 16-10-2019 16:54:40 0 (0x0000)
Find the boot drive (if any) [True] [10.0.18362.329] [False] LTIApply 16-10-2019 16:54:40 0 (0x0000)
New ZTIDiskPartition : \MININT-RU22TRD\root\cimv2:Win32_DiskPartition.DeviceID=”Disk #0, Partition #0″ \MININT-RU22TRD\root\cimv2:Win32_LogicalDisk.DeviceID=”V:” LTIApply 16-10-2019 16:54:40 0 (0x0000)
New ZTIDisk : \MININT-RU22TRD\root\cimv2:Win32_DiskDrive.DeviceID=”\\.\PHYSICALDRIVE0″ LTIApply 16-10-2019 16:54:40 0 (0x0000)
Found bootable drive (No Boot File Test) [ V: ]: \MININT-RU22TRD\root\cimv2:Win32_LogicalDisk.DeviceID=”V:” LTIApply 16-10-2019 16:54:40 0 (0x0000)
Ready to Prepare boot partition: V: LTIApply 16-10-2019 16:54:40 0 (0x0000)
Property UILanguage is now = en-US LTIApply 16-10-2019 16:54:40 0 (0x0000)
About to run command: cscript.exe //nologo “D:\Deploy\Scripts\ztiRunCommandHidden.wsf” “”D:\Deploy\Tools\X64\BCDBoot.exe” F:\windows /l en-US ” LTIApply 16-10-2019 16:54:40 0 (0x0000)
Command has returned: 19 LTIApply 16-10-2019 16:54:41 0 (0x0000)
FAILURE ( 5616 ): 19: Verify BCDBootEx LTIApply 16-10-2019 16:54:41 0 (0x0000
As you can see the command being executed was: cscript.exe //nologo “D:\Deploy\Scripts\ztiRunCommandHidden.wsf” “”D:\Deploy\Tools\X64\BCDBoot.exe” F:\windows /l en-US “
So instead of the “0x80004005” error code the error became a little bit more specific, since the command above returned error code 19 and “FAILURE ( 5616 ): 19: Verify BCDBootEx”
Time to do some further testing:
After the Task Sequence fails, we luckely can open a command prompt and start testing, at the command prompt we executed the same command with the /v switch for verbose mode 🙂 – you can find the command line options for BCDBoot.exe here: https://docs.microsoft.com/en-us/windows-hardware/manufacture/desktop/bcdboot-command-line-options-techref-di
X:\Deploy\Tools\x64>bcdboot.exe F:\Windows /l en-US /v
BFSVC: ServiceBootFiles MuiOnly:n Res:y Fonts:y BootMgrOvw:n BootStatOvw:n DbgTrn:y SuspendBDE:n
BFSVC: Using source OS version a000047ba0001
BFSVC: Copying boot files CopyBootManager(Yes) F:\Windows\boot\EFI -> \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot
BFSVC: Creating Recovery directory.
BFSVC: Logging boot file servicing to bootstat log \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\BOOTSTAT.DAT.
BFSVC Warning: Failed to log servicing event to bootstat \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\BOOTSTAT.DAT. Status: 0x80000005
BFSVC: Copying font files from F:\Windows\boot\Fonts to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\Fonts…
BFSVC: Copying resource files from F:\Windows\boot\Resources to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\Resources…
BFSVC: Servicing debugger files
BFSVC: Copying boot debugging files from F:\Windows\system32 to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot (kd__.dll)
BFSVC: Copying boot debugging files from F:\Windows\system32 to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot (kdstub.dll)
BFSVC: Done servicing debugger files.
BFSVC: BfsInitializeBcdStore flags(0x0000000c) RetainElementData:n DelExistinObject:n
BFSVC: VolumePathName for F:\Windows is F:\
BFSVC: Opening template from \Device\HarddiskVolume9\Windows\System32\config\BCD-Template.
BFSVC: BCD Error: File is not system store. File: \Device\HarddiskVolume7\EFI\Microsoft\Boot\BCD Status: 0
BFSVC: BCD Error: Failed to open system store. Status: c0000098
As you can see, BCDboot failed to open the System Store.
Let’s do some more testing with the command line options, in order to see if that helps:
Run BCDBoot.exe with the option to specify the volume letter (/s) and specify the firmware type (/f).
X:\Deploy\Tools\x64>bcdboot.exe F:\Windows /l en-US /s V: /f ALL /v
BFSVC: ServiceBootFiles MuiOnly:n Res:y Fonts:y BootMgrOvw:n BootStatOvw:n DbgTrn:y SuspendBDE:n
BFSVC: Using source OS version a000047ba0001
BFSVC: Copying boot files CopyBootManager(Yes) F:\Windows\boot\PCAT -> \?\GLOBALROOT\Device\HarddiskVolume7\Boot
BFSVC: Unable to open file \?\GLOBALROOT\Device\HarddiskVolume7\Boot\bootmgr for read because the file or path does not exist
BFSVC: Logging boot file servicing to bootstat log \?\GLOBALROOT\Device\HarddiskVolume7\Boot\BOOTSTAT.DAT.
BFSVC Warning: Failed to log servicing event to bootstat \?\GLOBALROOT\Device\HarddiskVolume7\Boot\BOOTSTAT.DAT. Status: 0x80000005
BFSVC: Copying font files from F:\Windows\boot\Fonts to \?\GLOBALROOT\Device\HarddiskVolume7\Boot\Fonts…
BFSVC: Copying resource files from F:\Windows\boot\Resources to \?\GLOBALROOT\Device\HarddiskVolume7\Boot\Resources…
BFSVC: Servicing debugger files
BFSVC: List of debugger files is empty
BFSVC: BfsInitializeBcdStore flags(0x0000021c) RetainElementData:n DelExistinObject:n
BFSVC: VolumePathName for F:\Windows is F:\
BFSVC: Opening template from \Device\HarddiskVolume9\Windows\System32\config\BCD-Template.
BFSVC: Opening store from \Device\HarddiskVolume7\boot\BCD
BFSVC: Creating General objects.
BFSVC: Creating Resume object.
BFSVC: Creating MemTest object.
BFSVC: Creating OsLoader object.
BFSVC: OsLoader identifier: {d831c116-6216-11e9-99b4-ca2c466ae3f4}
BFSVC: Removing duplicate entries.
BFSVC: Removing duplicate object {d21712be-6216-11e9-99b4-ca2c466ae3f4}
BFSVC: Create BOOTMGR object RetainBootDefault:n
BFSVC: Setting {default} to {d831c116-6216-11e9-99b4-ca2c466ae3f4}
BFSVC: Cleaning up debugger settings.
BFSVC: ServiceBootFiles MuiOnly:n Res:y Fonts:y BootMgrOvw:n BootStatOvw:n DbgTrn:y SuspendBDE:n
BFSVC: Using source OS version a000047ba0001
BFSVC: Copying boot files CopyBootManager(Yes) F:\Windows\boot\EFI -> \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot
BFSVC: Creating Recovery directory.
BFSVC: Logging boot file servicing to bootstat log \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\BOOTSTAT.DAT.
BFSVC Warning: Failed to log servicing event to bootstat \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\BOOTSTAT.DAT. Status: 0x80000005
BFSVC: Copying font files from F:\Windows\boot\Fonts to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\Fonts…
BFSVC: Copying resource files from F:\Windows\boot\Resources to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\Resources…
BFSVC: Servicing debugger files
BFSVC: Copying boot debugging files from F:\Windows\system32 to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot (kd__.dll)
BFSVC: Copying boot debugging files from F:\Windows\system32 to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot (kdstub.dll)
BFSVC: Done servicing debugger files.
BFSVC: BfsInitializeBcdStore flags(0x0000021c) RetainElementData:n DelExistinObject:n
BFSVC: VolumePathName for F:\Windows is F:\
BFSVC: Opening template from \Device\HarddiskVolume9\Windows\System32\config\BCD-Template.
BFSVC: Opening store from \Device\HarddiskVolume7\EFI\Microsoft\Boot\BCD
BFSVC: Creating General objects.
BFSVC: Creating Resume object.
BFSVC: Creating MemTest object.
BFSVC: Creating OsLoader object.
BFSVC: OsLoader identifier: {d8c631aa-6216-11e9-99b4-ca2c466ae3f4}
BFSVC: Removing duplicate entries.
BFSVC: Removing duplicate object {d2691890-6216-11e9-99b4-ca2c466ae3f4}
BFSVC: Create BOOTMGR object RetainBootDefault:n
BFSVC: Setting {default} to {d8c631aa-6216-11e9-99b4-ca2c466ae3f4}
BFSVC: Cleaning up debugger settings.
BFSVC: Opening recovery store from \Device\HarddiskVolume7\EFI\Microsoft\Recovery\BCD
BFSVC: Creating General objects.
BFSVC: Create BOOTMGR object RetainBootDefault:y
Boot files successfully created.
Here you can see it seems to be succesfull, but unfortunately the system didn’t boot. Probably it was succesfull on the BIOS part, but failed on the UEFI part. And since the Surface Pro 6 boots UEFI only, that made sense.
And:
Execute BCDBoot and preserve the default Windows Boot Manager firmware entry and the OS boot entry in the Windows Boot Manager using /p /d
X:\Deploy\Tools\x64>bcdboot.exe F:\Windows /l en-US /p /d /v
BFSVC: ServiceBootFiles MuiOnly:n Res:y Fonts:y BootMgrOvw:n BootStatOvw:n DbgTrn:y SuspendBDE:n
BFSVC: Using source OS version a000047ba0001
BFSVC: Copying boot files CopyBootManager(Yes) F:\Windows\boot\EFI -> \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot
BFSVC: Creating Recovery directory.
BFSVC: Logging boot file servicing to bootstat log \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\BOOTSTAT.DAT. BFSVC Warning: Failed to log servicing event to bootstat \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\BOOTSTAT.DAT. Status: 0x80000005
BFSVC: Copying font files from F:\Windows\boot\Fonts to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\Fonts…
BFSVC: Copying resource files from F:\Windows\boot\Resources to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot\Resources…
BFSVC: Servicing debugger files
BFSVC: Copying boot debugging files from F:\Windows\system32 to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot (kd__.dll)
BFSVC: Copying boot debugging files from F:\Windows\system32 to \?\GLOBALROOT\Device\HarddiskVolume7\EFI\Microsoft\Boot (kdstub.dll)
BFSVC: Done servicing debugger files.
BFSVC: BfsInitializeBcdStore flags(0x0000110c) RetainElementData:n DelExistinObject:n
BFSVC: VolumePathName for F:\Windows is F:\
BFSVC: Opening template from \Device\HarddiskVolume9\Windows\System32\config\BCD-Template.
BFSVC: BCD Error: File is not system store. File: \Device\HarddiskVolume7\EFI\Microsoft\Boot\BCD Status: 0
BFSVC: BCD Error: Failed to open system store. Status: c0000098
BFSVC Error: BcdOpenStore failed with unexpected error code, Status = [c0000098]
We then tried to install the system using the original Windows 10 ISO, which also failed, see the output of setuperr.log below:
2019-04-18 12:02:49, Error [0x060126] IBS CallBack_ImageWasSelectedInUi: An error occurred while removing the MultiEdition key from the blackboard.[gle=0x00000490]
2019-04-18 12:04:19, Error IBSLIB BCD: File is not system store. File: \Device\HarddiskVolume2\EFI\Microsoft\Boot\BCD Status: 0[gle=0x00000002]
2019-04-18 12:04:19, Error IBSLIB BCD: BcdExportStore: Failed to open system store. Status: c0000098[gle=0x00000002]
2019-04-18 12:07:26, Error [0x064230] IBSLIB BFSVC: Failed to create a new system store. Status = [c00000a2]
2019-04-18 12:07:26, Error [0x0641b8] IBSLIB ModifyBootEntries: Error modifying bcd boot entries. dwRetCode=[0x13][gle=0x00000013]
The solution:
Since we could install some machines over and over again, while other started failing all of the sudden we didn’t expect the UEFI settings directly.
The documentation is also very high-level and doesn’t give any in-depth information about the ins- and outs of certain settings: https://support.microsoft.com/en-us/help/4023531/surface-how-to-use-surface-uefi.
At first we thought of updating the EUFI firmware, but couldn’t find an option to do this while out of the Booted OS, since firmware for the Surface Pro 6 is supplied via MSI files or via Windows Update by Microsoft
In the end, it turned out that the setting called: “Enable boot configuration lock“, was causing the issue. While at first it seems that this option allows you to define the order in which devices boot, it really locks the configuration in the UEFI, not even giving access to the BCDBoot.exe tool.
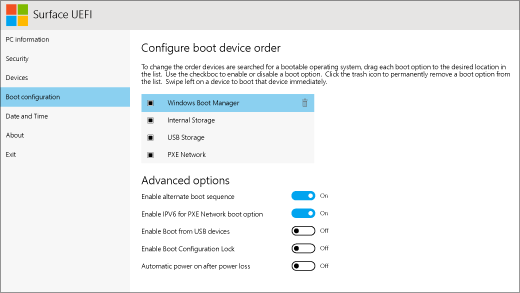
So for now, when encountering this issue, (which is not consequent) we are disabling the “Enable boot configuration lock” option, install the OS using USB and enable the option again just before the OS boots for the first time. We needed to go into the UEFI settings already to enable and disable Secure Boot already, since we couldn’t boot the USB with Secure Boot enabled.