When you decide to install Applications during your OS Deployment using Configuration Manager, there are some caveats which must be taken into account
Applications installed during a task sequence must be installed completely silent, that means that no user interaction is allowed.
Some points of attention are:
- Task Sequence runs in the context of the System account
- There is no Explorer.exe running during a Task Sequence
- Installation must be fully unattended, no user interaction is allowed
- The installer may never initiate a reboot, it should return return code 3010 for example when a reboot is needed. ConfigMgr will then take care of the reboot when needed.
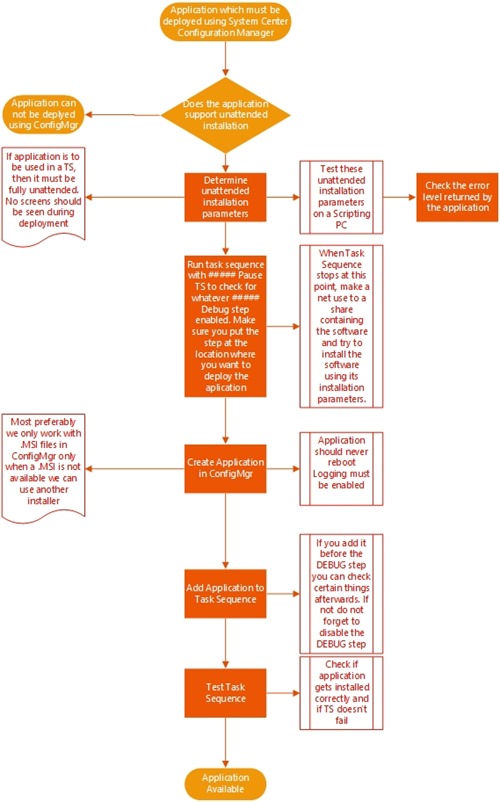
During many of my project building Task Sequences for customers I’ve build a way to test successful installation of an Application during a Task Sequence.
This is detailed in the Flowchart below:
Step 1: Intake of the application
During application intake, we collect all the information we can find for the application. In my opinion this information should be stored in a central place for example your DSL.
We need the following:
- Application Sources
- Installation Manual, which in the most ideal situation tells you exactly which parameters should be used for silent installation
- Application settings which you ideally determine together with the application owner, a senior user actually using the application.
We also need to determine the Name of the manufacturer, the name of the Application and the version
Step 2: Test Silent Application installation
First of all, you need to determine if the application has some requirements of other applications which should be installed for it to work correctly. Within ConfigMgr we can then install the required applications first before actually deploying the application we need.
Determine the silent installation parameters, some common parameters are listed below – but finding out the exact parameters can be a hard task. I really urge you to join the ITNinja community which has a lot of information about application packaging and unattended installation parameters.
Windows Installer
| Description | Option |
| Install the specified MSI | /i |
| Remove the specified MSI | /x=remove |
| Install to the C drive, not just the drive with the most free space | ROOTDRIVE=C:\ |
| Install silently with no user interface | /qn |
| Create a verbose a the path and filename specified | /l*v c:\windows\ccm\logs\<uniqueID>_<applicationname>.log |
| Do not allow the machine to be rebooted following installation | REBOOT=ReallySuppress |
InstallShield Legacy Setup
|
Description |
Option |
|
Execute the installation while recording any wizards responses in an ISS answer file at the specified name and path |
/r /f1 “path to ISS file” |
|
Run a silent installation using the specified ISS answer file |
/s /f1 “path to ISS file” |
|
Do not release the current session until the installation is complete |
/sms |
InstallShield Windows Installer Setup
|
Description |
Option |
|
Silently install and pass the specified parameters to be included Windows Installer Setup |
/s /v/qn”Windows Installer parameters” |
|
Description |
Option |
|
Install the specified MSI |
/i |
|
Remove the specified MSI |
/x=remove |
|
Install to the C drive, not just the drive with the most free space |
ROOTDRIVE=C:\ |
|
Install silently with no user interface |
/qn |
|
Create a verbose a the path and filename specified |
/l*v <location of logfile + name>.log |
|
Do not allow the machine to be rebooted following installation |
REBOOT=ReallySuppress |
Important: It’s important that you enable logging in your unattended application installation. ConfigMgr executes the installation parameters and determines successful installation based on the return code which is returned. Everything that happens in-between should be logged somewhere in order for you to determine what goes on during installation, and what went wrong when an application failed to install successfully.
Step 3: Test application installation in a Task Sequence
In all of my task sequences I created a run command line step named ##### Pause TS to check for whatever #### Debug which is disabled by default. This run command line step runs a script which pauses the Task Sequence allowing me to press F8 to start a command prompt from which I can test my application installation.
The script I use is listed below, I got this script from Niall Brady, who runs the Windows-noob website, another useful resource for SCCM related information. Save the code below in a .wsf script – keep in mind that you need to have MDT integrated (of course) in order to use the script. You Run command line step should contain cscript.exe <nameofscript>.wsf. If you put the script in your scripts folder of your MDT Files Package you will be able to execute it successfully.
<job id=”setEnv”>
<script language=”VBScript” src=”..\ZTIUtility.vbs”/>
<script language=”VBScript”>
Dim oTSProgressUI
set oTSProgressUI = CreateObject(“Microsoft.SMS.TSProgressUI”)
oTSProgressUI.CloseProgressDialog()
On error resume next
MsgBox “Pausing TS.”,0, “PAUSE”
</script>
</job>
From the command prompt, map a network drive to a place where you have stored the application, and try to run the application using the parameters you determined in step 2. Also make sure the logfile is created on the place you specified, and open the logfile in order to determine if application installation was successful.
Step 4: Create Application in ConfigMgr and test your task Sequence
When you can successfully install the application using the method described in step 3 its time to integrate your application installation in your common task sequence. Create the application as described in this article: Keep in mind that when you create the application that you enable the setting Allow this application to be installed from the Install task sequence action instead of deploying it manually and that you allow the application to be installed whether or not a user is logged on.
If you have the ##### Pause TS to check for whatever #### Debug still enabled you should disable this step again.
Test your task sequence with your new application added. After installation check both the AppEnforce.log (which details how the application installation was executed) and the logfile which you specified during your application installation in order to determine if application installation was successful.
Step 5: Test Application Deployment and Application uninstallation
Keep in mind that most applications that you create in ConfigMgr should also be deployed and uninstalled at some point in time. Make sure that you also test these scenario’s as well.
As a last note here are some things to consider as well:
First: Sometimes installing an application can trigger other application installations as well. Which could break your task sequence. Take for example the McAfee framework installation. This installation installs the McAfee agent, which contacts the McAfee ePO server. This server will then sent additional installations to the client based on set policy. Say for example that your task sequence is still running and installing applications, you can end up in a situation where the ePO server initiates an installation, and the next application which gets installed in the Task Sequence fails because another installation is already running (error code 1618)
Second: Most ideally you should separate application installation and application configuration from each other. Having this separation allows has several benefits. First of all you can include the application installation part in your Build & Capture task sequence, allowing the application to be configured in a second step when that image is deployed. Secondly you can have one application with different configuration based on a variable or specific location for example
Hi,
Thanks for sharing your informations about silent app,
I have couple of app who does not contain silent command. (confirm by owner etc…)
Then, what do you do with these app ?
Regards.
Hi TixTix,
I nothing helps, then there is AutoIT to the rescue.. dirty way, but it gets the job done
Technically you can do an interactive install during a task sequence. It isn’t supported out of the box, but it is possible with a bit of hacking. I’ve done this under some extreme circumstances where we needed a task sequence for security kiosks which run camera software. Unfortunately the camera software isn’t enterprise friendly and we don’t use 3rd party packaging tools. I used a combination of AutoIT and psexec to get it to work. It was a bit of a beast to test, but I was eventually able to make it work.
To add SCCM applications, Office Suite, Add to collection, Add to AD group, Add primary user and more; use SCCM Task Sequence OS Deployment Orchestrator.
It’s free and enterprise grade. https://sccmtspsi.com/
A Just to mention a few benefits:
– Detailed email reporting of task sequence deployments.
– Unlock Bitlocker (Active Directory, remote Active Directory, MBAM, file & key)
– OnDemand task sequence selection.
– Operating system selection
– Office application selection.
– SCCM application selection.
– SCCM collection membership in real-time.
– Active directory group membership.
– Add Primary system users.
– Save and restore user data (USMT).
– 18 extension attribute assignments.
– Automatic staging.
– Decommissioning.
Documentation : https://sccmtspsi.com/documentation/