In my deep dive article on Office 365 Advanced Threat Protection (ATP) I mentioned that Microsoft provides best practices as described in the following article: “Recommended settings for EOP and Office 365 ATP security“. When implementing the settings in the article you either have the option to go for a “Standard” or “Strict” security level, and you can check your environment towards these best practices using the Office 365 ATP Recommended Configuration Analyzer (ORCA).
After returning from my holiday this year, I noticed a welcome addition to the Threat Management Policy page in the Office 365 Security & Compliance center called “Templated Policies”, for now the section Templated policies contains one section called “Preset security policies”
Templated policies are based on Microsoft recommendations and current attack trends. As the threat landscape changes, these policies can be automatically updated by Microsoft. You can immediately implement these policies, and they will always adhere to Microsoft’s latest recommendations.
A preset security policy is compilation of settings for all security policies: anti-spam, outbound spam filter, anti-malware, anti-phishing, ATP Safe Links, and ATP Safe Attachments.
Having these templates available is in line with other products where Microsoft is creating templates which you easily implement in order to secure your environment, just like the Security Defaults in Azure Active Directory, which I described in my article: “Microsoft deprecates Conditional Access baseline policies in favour of Security Defaults, here is what you need to know and do“.
Preset security policies
Microsoft provides “Standard” en “Strict” protection profiles which eventually implement the settings as described by Microsoft’s best practices. They are not configurable from a settings perspective.
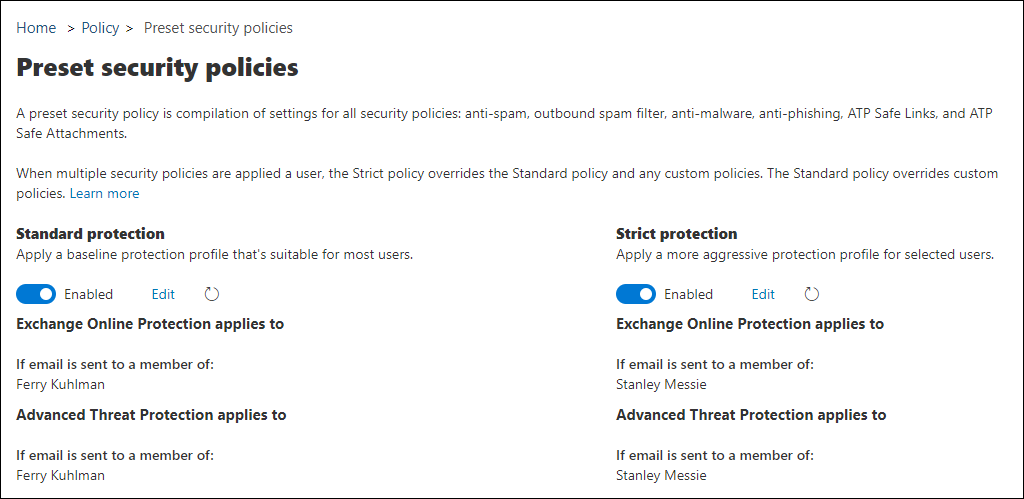
For each protection profile you have the following options:
- Enable or disable the policy
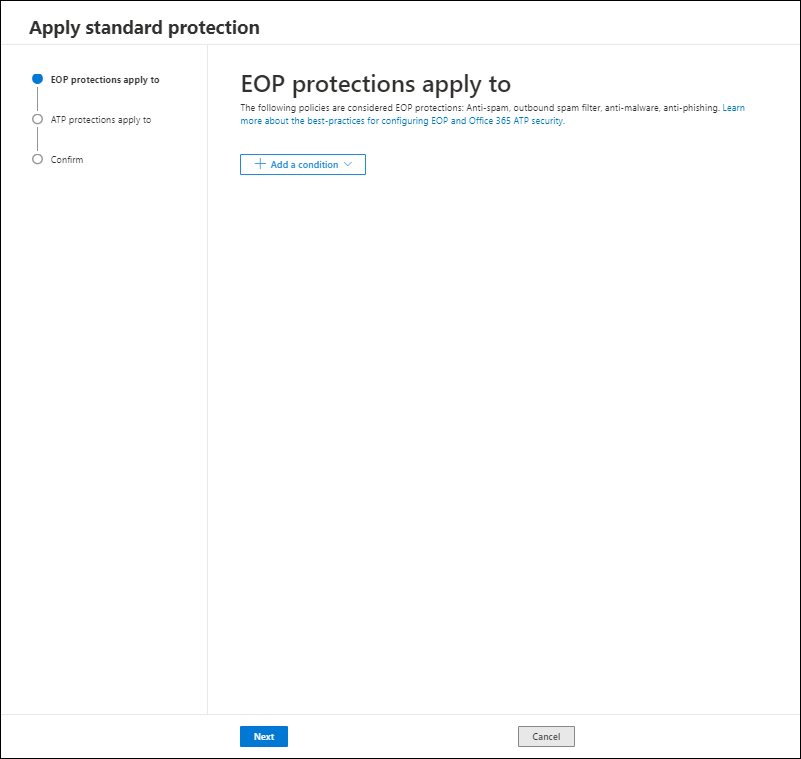
- Define to whom the EOP protections apply using conditions
- Define to whom the ATP protections apply using conditions
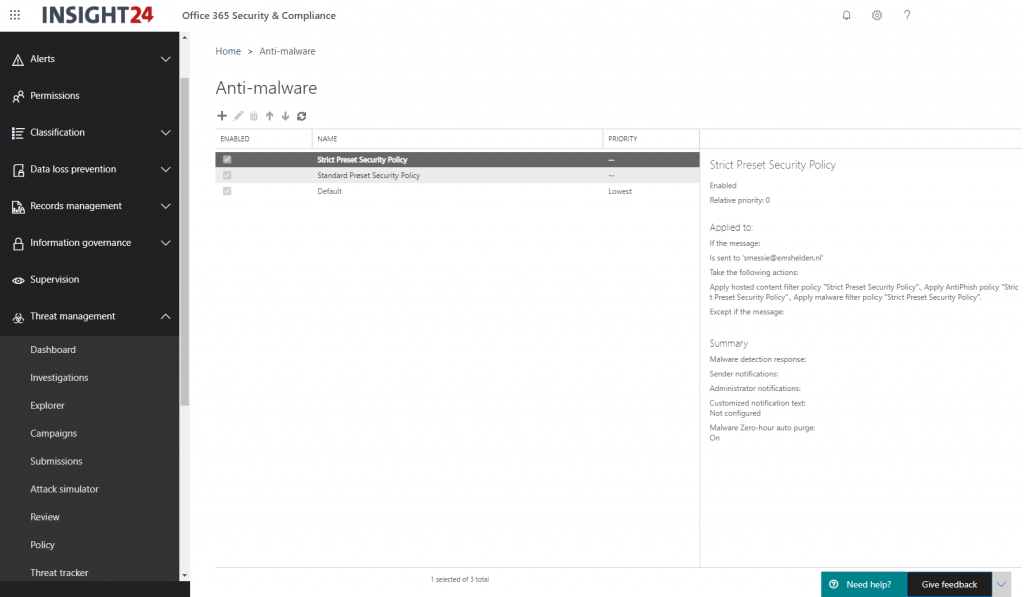
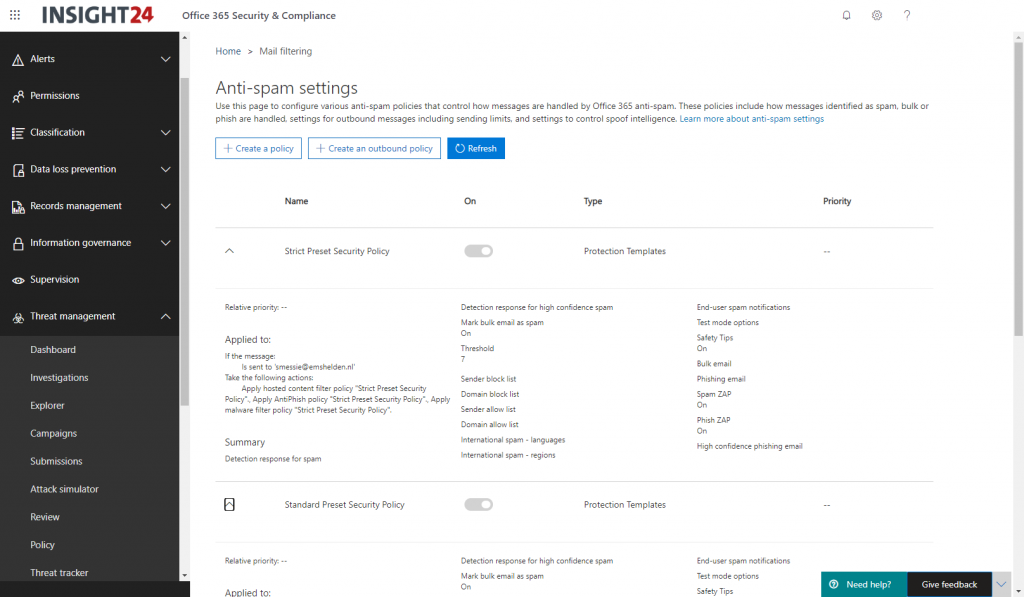
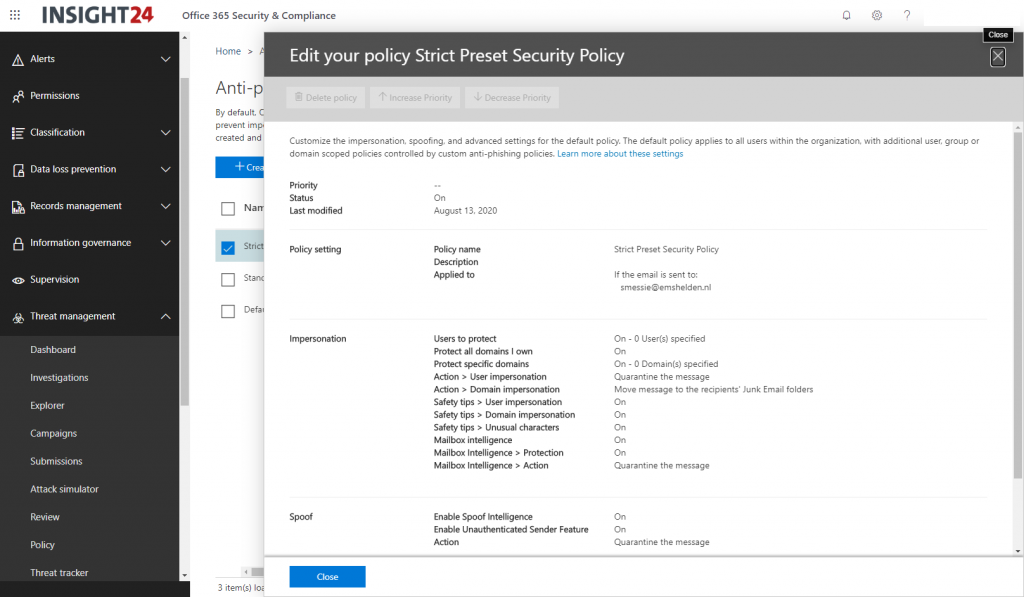
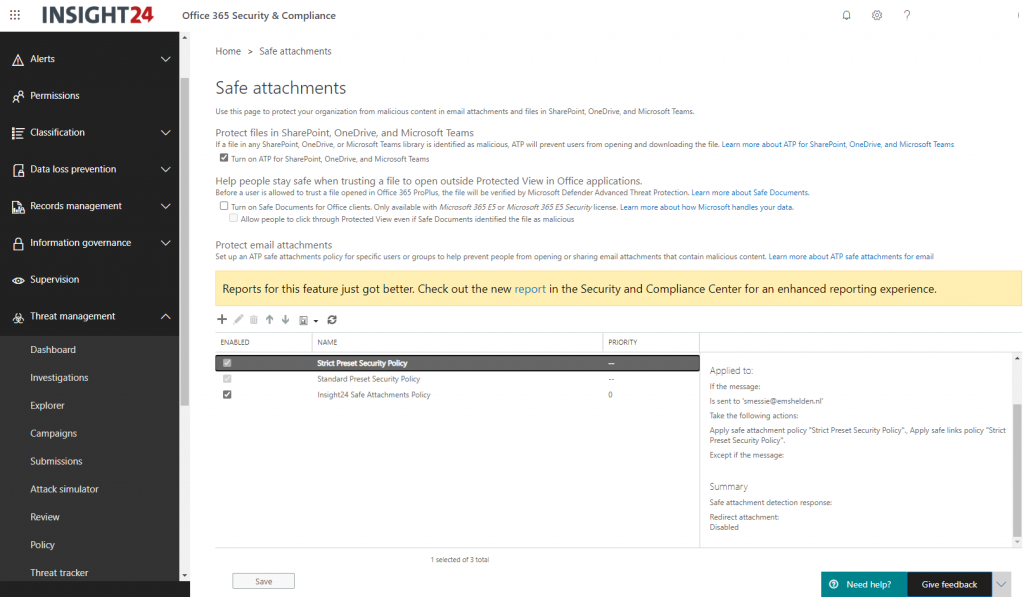
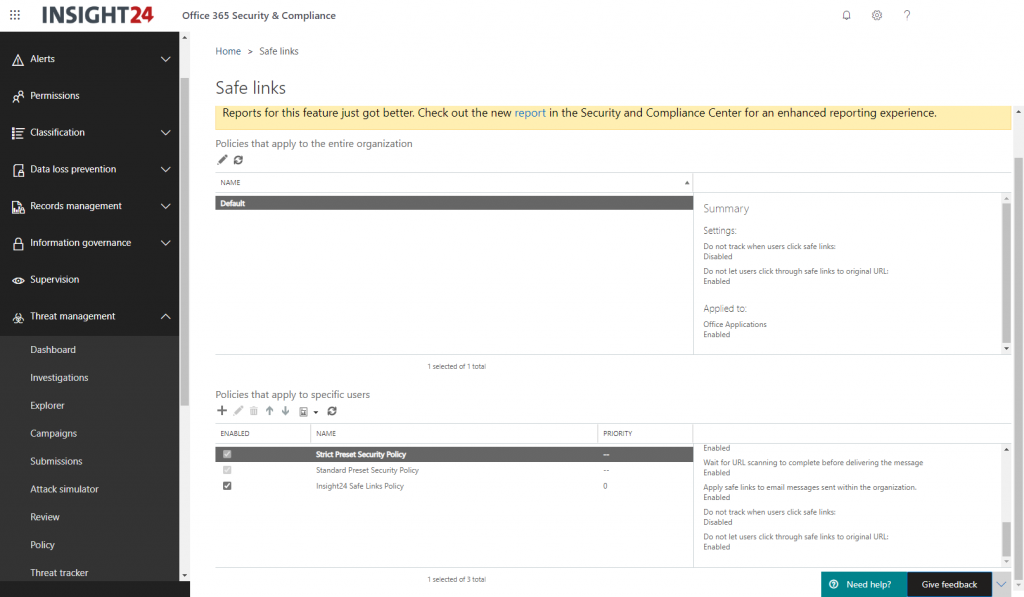
Once enabled the following policies will be created, named Standard Preset Security Policy and Strict Preset Security Policy under each configuration node.
Exchange Online Protection
- Anti-Spam
- Anti-Malware
- EOP Anti-phishing policies
Office 365 Advanced Threat Protection
- ATP Anti-phishing policies
- Safe Links policies
- Safe Attachments policies
Note: When you enable the policy, and later disable it again, the policies remain in the configuration but will be in a disabled state.
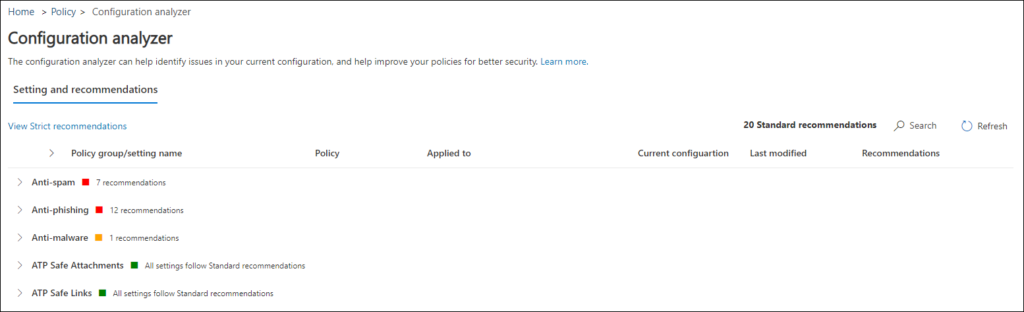
Configuration Analyzer for protection policies
With the templates Microsoft also released the Configuration Analyzer for protection policies in EOP and Office 365 ATP in preview. Configuration analyzer in the Security & Compliance center provides a central location to find and fix any of your security policies that contain settings that are below the Standard protection and Strict protection profile settings in preset security policies.
Unfortunately the Configuration Analyzer was not active yet in either of my tenants, once available I’ll update this article. For the time being, the following article provides an idea of what is does: Configuration analyzer for protection policies in EOP and Office 365 ATP
Update October 2020: In the meantime this functionality is available within tenants.
Conclusion
Templated policies, and preset security policies are a welcome addition to Office 365. I would advise to use these templates on new Office 365 implementations right from the start. For organizations who already have security settings implemented you can either keep them and evaluate your policies against the best practices using ORCA/the Configuration Analyzer, or you can transition to the new policies, since the policies can easily be scoped to groups or specific users.
Disadvantage of using this option, is that if Microsoft modifies any setting, you might be surprised, you either need to keep an eye on announcements of Microsoft doing so, or live with the fact that this can happen. It will depend per organization.
References
Preset security policies in EOP and Office 365 ATP
Configuration analyzer for protection policies in EOP and Office 365 ATP