On Wednesday June 30, I spoke at the monthly user group meeting of the Microsoft 365 Security & Compliance user group. The Microsoft 365 Security & Compliance user group is based in the UK and UK based user group consists of Alan Eardley (@al_eardley) and Peter Rising (@M365Rising) The meeting will started with a very…
A first look at Azure AD Conditional Access authentication context
During Microsoft Ignite in March this year, Microsoft announced several new upcoming functionalities for Azure Active Directory. One of the announcement was the Azure AD Conditional Access authentication context, for which I that time I already wrote about what it could do in my blog article: Modern Workplace Management key takeaways from the Microsoft Ignite…
Announcing #WPNinjasNL Tuesdays Webinar #27 (Tomorrow), Tuesday June 22, featuring Peter Daalmans
For Tuesday, June 22 (yes, thats Tomorrow) we are proud to announce that our very own Peter Daalmans, Microsoft MVP Enterprise Mobility will host a session about: Ten practical tips to secure your corporate data with Microsoft 365 – 201906 edition Session abstract: Employees demanding access to your corporate data and apps on their often…
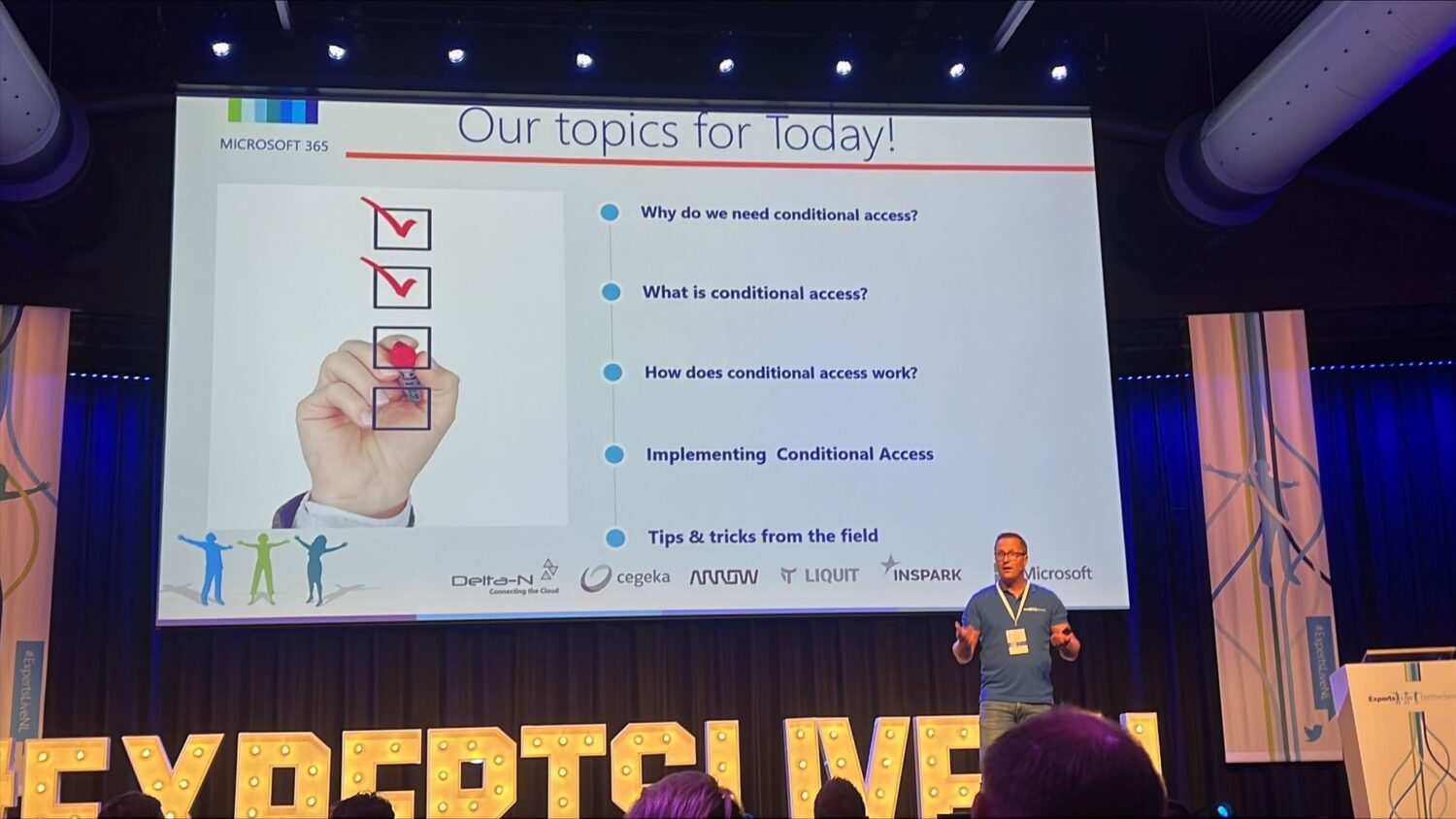
Speaking about Conditional Access at the Microsoft 365 Security & Compliance User Group on June 30, 2021
On Wednesday June 30, I will be speaking at the monthly user group meeting of the Microsoft 365 Security & Compliance user group. The Microsoft 365 Security & Compliance user group is based in the UK and UK based user group consists of Alan Eardley (@al_eardley) and Peter Rising (@M365Rising) The meeting starts at 18:00…
Announcing #WPNinjasNL Tuesdays Webinar #26, Tuesday June 8th, featuring Thorsten Pickhan and Michael Plettner
For next week, Tuesday, June 8th we are proud to announce that Thorsten Pickhan, Senior Microsoft UC Consultant and Michael Plettner, Microsoft MVP (Office Apps and Services will be hosting a session about: Teams Phone System – A must have for the modern workplace. Session abstract: Modern workplaces and flexible “offices” are important topics and…
Received the Microsoft Most Valuable Professional (MVP) award in Enterprise Mobility
On Thursday June 1st 2021, I received an email from Microsoft telling me that I received the Microsoft Most Valuable Professional (MVP) award. My award is given for the category Enterprise Mobility, which covers most of the topics part of the Microsoft 365 line of products. It’s a real honor to be recognized by Microsoft…
Our session about Modern Authentication at the May 2021 meetup of the Microsoft Cloud and Client Management Community #MC2MC
Yesterday, on Thursday May 27, Erik Loef and I delivered a session at the May virtual event of the Microsoft Cloud and Client Management Community. The Microsoft Cloud and Client Management Community is a Belgian community with the following members: Tim de Keukelaere, Wim Matthyssen, Tim Hermie, Ken Goossens, Jasper Bernaers, Peter de Tender, Peter…
A first look at using Filters for devices as conditions in Azure AD Conditional Access policies
Earlier this month I wrote an article about using filtering in assignments for apps, compliance policies and configuration profiles in Microsoft Endpoint Manager. And now Microsoft has made available a preview of “Filters for devices” for use in your Azure AD Conditional Access policies. Because this functionality is provided as a preview there is no…
MDM policy processing on Windows 10 with Microsoft Endpoint Manager, a closer look
The goal of this blogpost is to explain more about what happens between the moment that a configurations setting in Microsoft Endpoint Manager (MEM) are created or modified and applied from that point forward to the endpoint. I will cover the options available to validate and monitor if the settings make it to the endpoint,…
Announcing #WPNinjasNL Tuesdays Webinar #25, Tuesday May 25, featuring Jan Bakker
For next week, Tuesday, May 25 we are proud to announce that Jan Bakker, Microsoft 365 Consultant and Microsoft Enterprise Mobility MVP will be hosting a session about: All about Azure MFA. Session abstract: In this session you will learn all about Azure MFA. We take a look at the different ways to do a…
Announcing #WPNinjasNL “Live – Ask us Anything” #5, on Tuesday May 18, 2021 (Tomorrow) about Endpoint Analytics
On Tuesday, May 18 we are proud to announce our fifth “Live – Ask us Anything” session, hosted by Ronny de Jong and Frans Oudendorp. The topic for this session will be about: Endpoint Analytics During this session Ronny and Frans and special guest Albert Cabello Serrano, Principal Program Manager Lead at Microsoft will go…
A first look at filtering when assigning apps, compliance policies and configuration profiles in Microsoft Endpoint Manager
Microsoft is currently in the process of rolling out a preview of filtering for apps, policies and profiles in Microsoft Endpoint Manager. With this new functionality you will be able to define extra applicability conditions for Apps, compliance policies and configuration profiles. Not every workload is supported (yet) though, for example you cannot use the…
A first look at expediting Windows 10 Quality Updates when using Windows Update for Business and Microsoft Endpoint Manager
During Microsoft Ignite, Microsoft announced the option to bypass pre-configured Windows Update for Business policies to immediately deploy a security update across your organization when emergencies arise as part of their Windows Update for Business deployment service. Today, Microsoft has made available a preview of possibility to expedite the installation security patches as part of…
Speaking about Modern Authentication at the May 2021 meetup of the Microsoft Cloud and Client Management Community #MC2MC
On Thursday May 27, Erik Loef and I will speak at the May virtual event of the Microsoft Cloud and Client Management Community. The Microsoft Cloud and Client Management Community is a Belgian community with the following members: Tim de Keukelaere, Wim Matthyssen, Tim Hermie, Ken Goossens, Jasper Bernaers, Peter de Tender, Peter Linders and…
Announcing #WPNinjasNL Tuesdays Webinar #24, Tuesday May 11, featuring Nico Zieck
For next week, Tuesday, May 11 we are proud to announce that Nico Zieck, Director Technology & Solutions at Liquit B.V. will be hosting a session about: Top 5 biggest technical hiccups when moving to the cloud. Session abstract: The question is no longer why you should move to the cloud. The benefits are clear!…